Here’s the Best Tools for Windows NTFS Permission Auditing and Reporting – [ Analyze Active Directory, Shares, Files/Folder and More with These DOWNLOADS! ]
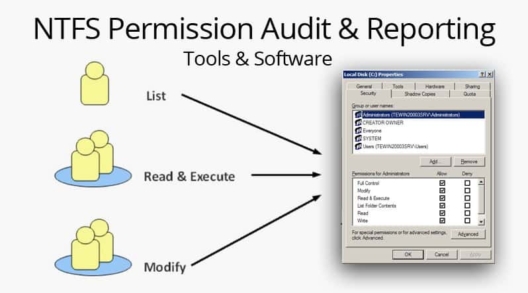
The Best Windows NTFS Permission Auditing & Reporting Tools
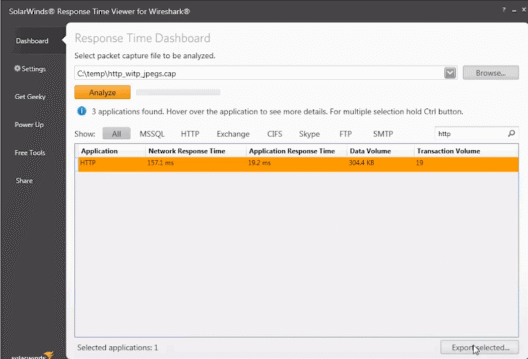
Analysis of Wireshark Response Times using a Free TOOL – Tutorial!
Solarwinds’ Response Time Viewer for Wireshark is a standalone tool that analyzes the packets captured by Wireshark, so you can get in-depth information about your network in a dedicated viewer. This tool is a great one for troubleshooting network problems as you can analyze most common packet formats. Typically, you should use Wireshark for capturing […]
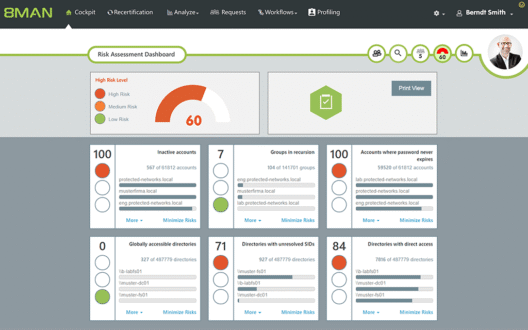
Access Rights Manager Review – How to Audit AD Permissions, File Shares & More!
/ August 25, 2023 — SecurityAuditing Active Directory, File Permissions, File Shares and More is Now Easier than Ever from a Centralized Location using Solarwinds Access Rights Manager, Here’s why!
Port Scanners for Scanning Windows/Linux Systems for Open Ports/Service
Port Scanners are an important tool when you want to investigate any remote or local network for security considerations. Used by programmers and network administrators, these port scanners are used to mainly know what ports are being used by what applications, so you can identify malicious programs right away. These port scanners can also be […]
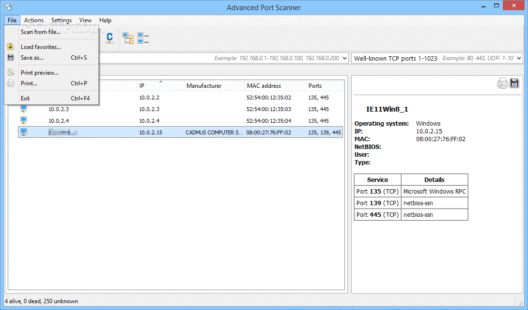
Advanced Port Scanner – A Review of one of the Top Port Scanning Tools on the Market
/ December 14, 2022 — SecurityAdvanced Port Scanner is a Versatile Port Scanner that is 100% FREE – You can scan local networks and remote Networks (LAN & WAN) Fast & Free from Any computer!
Visualizing Network & Bandwidth Activity with GlassWire
GlassWire is a new type of graphical network monitor for Windows that focuses on endpoint monitoring. The software runs on Windows 7, 8, and 10, and there is also a version of the app for Android. Setting up GlassWire for Windows is fairly simple and only requires using a Windows installer that can be downloaded […]
The Best Network Security Software & Frameworks for Pen-testing & Vulnerability Assessment
Finding Vulnerabilities and Exploits/Holes in your network infrastructure should be something you Do before a Hacker finds them – We’ve highlighted the Top Tools for Network Security Assessment, Vulnerability Scanning and much more!
WordPress Security and Available Plug-ins
WordPress is one of the most popular website platforms for bloggers and businesses as of 2017. It is easy to use and flexible as well as highly supported by developers and designers, but its security should also be considered. WordPress Security Issues It is a sad fact that a great many websites have been hacked […]
Nmap Port Scanner
Nmap is a free port scanner you can use to audit your own network and ensure the security of your hosts from outside your firewall as well. It is also entirely likely that your external interfaces are being scanned at this very moment with Nmap, or tools like it. One cool thing about Nmap, is […]
New Worm that Doesn’t Need Attachment
There is a new bagle worm that uses an exploit in IE. It does not need to have the user open an attachment, they just need to read an email with HTML in it. !!! There is a test to see if you are vulnerable here: http://secunia.com/MS03-032 More detailed info here: href=http://secunia.com/advisories/9580/ Bagle Q info […]
Baseline Security Analyzer
Do check out the Baseline Security Analyzer tool from Microsoft. Just download the MSI package from the page and install it with a shortcut on the Desktop (default). We ran it against a fresh Windows 2000 install with just SP2 installed. Here is a screenshot of the results. We are alerted to many security issues. […]
Verifying File Integrity with MD5 Checksums
We use MD5deep, because it has a recursive option which we discuss in this article. For now, though, we are just going to cover how to verify the MD5 checksum on a file. Grab the MD5 checksum from a site authoritative for your software package, and grab the software from a mirror site. Of course, […]
Quick and Dirty Host Block
If you are being attacked or abused by a particular host, just enter the following command to deny all access to the host: /sbin/route add -host <ip address> reject Replace with the IP address of the host you want to block. The address will stay blocked until you bounce the interface. Alternatively, you could allow […]
Using MD5deep To Verify Tree Integrity
We talked a little about MD5deep in this article. One nice thing about MD5deep is that it can do recursion. This allows you to create a set of MD5 sums for an entire directory. /etc is a good one to use as an example. Let’s create the set of MD5 sums: root@srv-1 etc # md5deep […]
Virus Test File
Check out the European Institute for Computer Anti-Virus Research (eicar) Anti-Virus Test File page. EICAR provides test files you can send to your users to determine if their anti-virus software is functioning correctly. We’ve seen this work fine on Trend Micro and Norton Anti-Virus software, but most ant-virus software should correctly detect these files. To […]
Compiling PGP 2.6.2
This is certainly an old topic, but I always forget how to compile PGP 2.6.2 on GNU/Linux. Grab the source from MIT, probably, is what you want. You may also want to consider gpg. Much has changed since 1994! PGP 2.6.2 is particularly interesting for keeping password files using conventional encryption. It is possible to […]
A Trojan in Every Port
If you have any kind of intrusion detection set up like Psionic’s PortSentry or a personal firewall, you’ll see attempts to connect on ports you may not be familiar with. Even looking up the port in /etc/services doesn’t tell the whole story. To find all known network services, trojans, worms and exploits associated with a […]
Linux Kernel Exploit
There is a local user privilege exploit for the Linux kernel. Details are here: http://isec.pl/vulnerabilities/isec-0021-uselib.txt One thing to remember is that a local user does not mean that the user has to have access to the physical machine. It means that any user that can run code on the machine can gain root access.
Keylogging
Like anything else, keylogging can be used for good, or for evil. Here is a list of related links, including both hardware and software keyloggers. (Yow!) Regardless of the privacy issues, there are also security issues as well. Some trojans will install keylogger software as part of their kit. There are also keyloggers geared for […]
Automating Secure FTP Downloads With Kermit
If you need to automate FTP downloads, and want lots of flexibility, an oldie but goodie is Kermit. I know what you’re thinking: “Hey, isn’t Kermit an old DOS comms program?”. Yes, it is a very old program. The cool thing about this, though, is that if you need to automate file transfers, it has […]