Today, most people use removable devices to transfer data from one system to the other. The best part about removable devices is you can easily carry important files along with you to any location and do not require an internet connection to share files. Despite having so many benefits, they are still labeled as a security risk.
Cybercriminals often target these miniature hard drives to inject malware and spread it across the network. These lightweight, portable USB flash drives are used in most companies for managing backup and storing confidential data. Hence, attackers often target them to access sensitive data and make their way into the system. In some cases, unsecured or failed USB drives also cause data leakage.
Data security of USB drives is one of the biggest challenges that most companies face in today’s work environment. There have been many cases in the past related to USB device misuse and data leak. Hence, it has become crucial for businesses to implement best practices to protect their data and strengthen security.
Here, we will discuss different practices and ways to Lock Flash Drives with Endpoint Protector.
CoSoSys Endpoint Protector and its Features
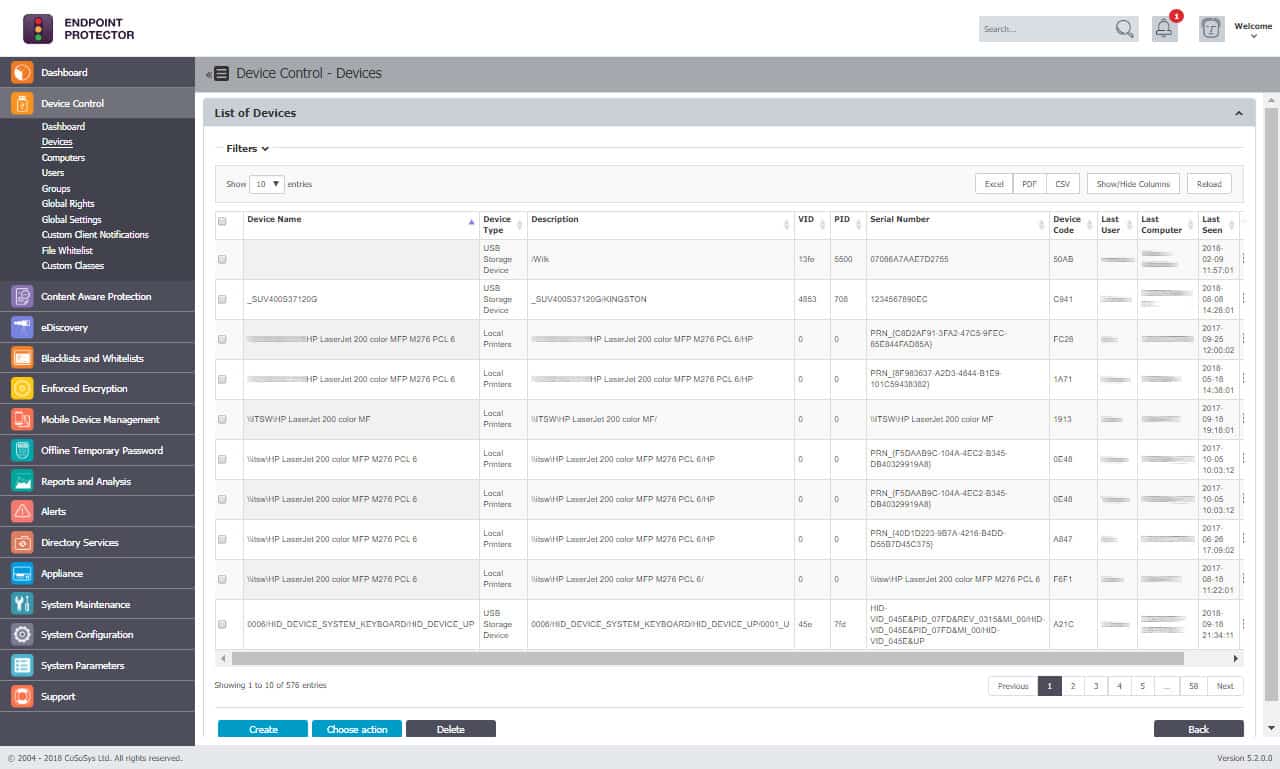
Endpoint Protector is a trusted Data Loss Prevention (DLP) solution that monitors and controls portable storage devices, such as USB drives, and prevents theft and data leaks. It has a device control feature that helps users remotely monitor USBs and peripheral ports, shares a list of devices that can or cannot be used, and defines policies for uninterrupted workflow.
Key Features:
- Military-grade encryption
- Offline Temporary Access Administrator
- Content-Aware Protection
- Generates log reports
- Statistics module for filtering data to get deeper insights
- File Tracing
- File Shadowing
- Instant alerts for Sensitive Content Transfers
- Organize and cleans unnecessary files
- Stealth Mode and Transparent Mode
Why do we recommend it?
During our hands-on testing, Endpoint Protector’s military-grade encryption and content-aware protection were standout features. We installed the solution and were immediately impressed by the granular control it offers over USB ports and peripheral devices. However, organizations with less tech-savvy users might find the array of features a bit overwhelming at first.
With the help of Endpoint Protector by CoSoSys, businesses can easily get control of the USB ports and prevent data loss. Further, it blocks unauthorized devices and prevents any malware or virus from spreading throughout the network.
The platform also supports advanced security solutions such as Enforced Encryption and EasyLock. The EasyLock feature provides 256bit AES Military Strength Data Encryption that acts like a vault and offers full-time protection to the data stored in it via encryption.
Further, this feature is paired with enforced encryption, i.e., an encryption and decryption program that automatically runs whenever a user plugs in the USB storage device to a system. It has a password-protected encrypted area that ensures users that the data will continue to remain safe even if it is lost or stolen.
Who is it recommended for?
Endpoint Protector is an ideal solution for enterprises that need robust Data Loss Prevention (DLP). It’s particularly beneficial for organizations handling sensitive data, such as healthcare providers, financial institutions, and government agencies. The tool’s support for multiple operating systems, including Windows, Mac, and Linux, makes it versatile for mixed-environment networks. Moreover, its strict policy enforcement capabilities make it a good fit for businesses transitioning to remote work, as it provides consistent data protection regardless of location.
Overall, Endpoint Protector is an industry-leading cross-platform ideal for networks of any architecture. It protects the entire network regardless of the operating system, including Windows, Mac OS X, or Linux. You can quickly generate reports and track USB activity on all endpoints with the help of this powerful solution.
Why choose Endpoint Protector?
There are various reasons why most enterprises choose Endpoint Protector to lock flash drives. The device-controlling tool is quick and easy to install. Further, it provides centralized management and excellent security features that ensure the data is safe at all times.
Users can easily lock unauthorized devices or users as per the computer-based and user-based policies supported by the tool. Additionally, the platform allows businesses to keep track of all USB activities and content movement.
Since a lot of data moves around the corporate network, managing them manually can be challenging. It is important to invest in a tool that automatically monitors all activities and prevents data leaks. Also with Endpoint Protector, you can trace, monitor, and control all transfers from plugin USB drives.
It supports alert features that update users immediately on noticing suspicious activities. They trigger an email sent to administrators updating on sensitive content transfers.
Further, after plugging the device into the system, the tool automatically scans the content and identifies sensitive data at the endpoint level to prevent data breaches.
Overall, many benefits make Endpoint Protector a great solution for various businesses.
How Does Endpoint Protector Device Control Work?
Device Control Tools are essential for organizations that want to control and manage the use of USB flash drives and other removable storage devices. These tools provide granular access rights and enforced security that protects the entire network. Here is how the Endpoint Protector works and controls the USB devices:
- Lock or Block Unauthorized users or removable media The Device control module immediately blocks Bluetooth connections, and USB and peripheral ports and notices any risk coming with them. Based on the encryption level, it allows only removable devices with a high level of security to connect endpoints and share files. In fact, in some cases, companies encourage employees to seek an alternate solution to transfer files. However, it can be risky too. Apart from the device control module, the tool also supports a content-aware protection module that restricts USB drives rather than locking them entirely.
- Granular policies The policies supported by the tool are not only restricted to the devices, but they can be modified and created for individual groups, users, or computers. As a result, with the help of Endpoint Protector, businesses can enforce stricter security controls for sensitive data. Also, they can try blocking removable devices for all except a few specific departments and users to perform regular tasks. Enterprises can also practice the read-only setting that allows users to only read files and block transfers to and from the removable devices.
- Strict Policies for Remote Work Many businesses started operating from home during and after the pandemic. As a result, the risk of data loss and cybercrime increased by 300%, as per a report. However, there are tools like Endpoint Protector that continue to provide strict security regardless of whether your work device is in the office or at home. Companies can also enforce stricter removable media policies and set different rules based on their requirements with Endpoint Protector.
- Offline Temporary Passwords There are cases when you need to quickly transfer or view files and employees are absent or not available in the office. For such cases, Endpoint Protector has a feature that allows temporary unrestricted access to a specific device or user.
How can Endpoint Protector Help Businesses?
By choosing Endpoint Protector for your business, you can add a layer of security to the entire network. It has various features like enforced encryption and EasyLock that encrypt and allow only authorized users to transfer sensitive data. Hence, ensuring that the data remains safe even if it is lost or stolen by the attackers.
Further, it maintains compliance with HIPAA, PCI DSS, SOX, and other regulations. Another plus point that makes Endpoint Protector a great DLP solution for businesses is it keeps the data secure and reduces the chances of Data leakage or loss with the use of enforced encryption.
With so many features and advanced security solutions, employees can easily focus on other areas of business.
Conclusion
Almost everyone uses Flash drives and other removable media devices to transfer data from one source to the other because it is easy to use and quick. But, we often miss out on the security risks. It is true that transferring files via flash drives is easy and requires no internet connection. But, still, there are risks, such as attackers can easily inject malware into your system through that miniature drive leading to data leak or theft.
Unsecured or failed USB drives can also cause data leakage. Hence, to protect your confidential data, businesses use different tools and platforms like Endpoint Protector by CoSoSys. Endpoint Protector is a leading Data Loss Prevention (DLP) solution with military-grade encryption that monitors, encrypts, and blocks unauthorized flash drives and other removable media devices.
Its Enforced Encryption and EasyLock act as a vault and ensure that the data within it will remain safe even if it is lost or stolen. Regardless of the operating system, including Windows, Mac OS X, or Linux, the tool protects the entire network and tracks USB activity on all endpoints.
It has some of the advanced features that make it an ideal platform for networks of any architecture. Further, businesses can enforce stricter security controls for sensitive data with the help of Endpoint Protector.
Endpoint Protector maintains compliance with HIPAA, PCI DSS, SOX, and other regulations as well as keeps the data secure and reduces the chances of Data leakage with its enforced encryption. Its Device Control module ensures that all the storage devices used by third-party or organizations are encrypted.
Daily, a lot of data is moved or transferred around the corporate network. Hence, to protect your system from malware injection or other threats, it is essential to invest in a tool that can trace, monitor, and control all transfers after plugin USB drives.
If you are looking for a tool that will also lock flash drives on noticing any risk coming with them, we recommend Endpoint Protector by CoSoSys.