As more and more organizations are deploying workloads to the cloud, in a way, they are extending the use of legacy networks and security. Excessive use of legacy firewalls and VPNs leads to creating a mesh network that is difficult to implement and manage. Additionally, it also leads to an increase in the security risk.
Thus, to protect your cloud data, devices, and containers from such challenges and risks, most companies depend on tools like zScaler Cloud Protection that provide full protection to public cloud assets and reduce the risk of exposure. It further helps eliminate operational complexity out of cloud workload security.
Here, we will discuss zScaler Cloud Protection in detail. We have also listed a few alternatives to zScaler Cloud Protection in case of a change of mind businesses can trust and invest in these cloud security solutions.
zScaler Cloud Protection Product Overview
zScaler Cloud Protection is a cloud security platform trusted by several high-profile companies for public cloud assets and data protection. The rise in cloud computing services has also increased the risk of exposure and threat. But, with the help of this easy-to-manage, simple cloud security tool, you can protect your business against malware and other threats.
Key Features
- Advanced threat protection
- Supports data loss prevention controls
- Provides unparalleled flexibility
- A scalable and reliable cloud security solution
- Secures workload communications
- Behavioral Analytics
- Compliance Management
- Vulnerability Scanning
- Intrusion Detection System
- Zscaler Workload Segmentation
- Offers Simplified Connectivity
- No Lateral Movement
- Zero Attack Surface
- Secures cloud security posture.
- Protects user access to cloud workloads
- Offers Identity-based protection
Why do we recommend it?
During our hands-on testing of zScaler Cloud Protection, we were especially impressed by its advanced threat protection and vulnerability scanning features. We installed the platform and navigated its interface to validate its claim of easily securing all cloud data and workloads, and we can confidently say it lives up to expectations.
zScaler Cloud Protection is an integrated platform of cloud services that helps eliminate operational complexity out of cloud workload security and secures all workload configurations and permissions.
zScaler Cloud Protection is designed with flexible scalability and provides better cloud-based security. The main purpose of designing the platform was to secure your cloud workloads and data across cloud and data center environments without affecting the performance and causing any delay.
It enables organizations to eliminate lateral threat movement within VPCs and automatically respond to blocks.
Minimize business risk and improve productivity with the trusted zScaler Cloud Protection platform. The purpose-built cloud platform supports deep inspection and allows administrators to verify access rights based on identity and context to keep the attackers away from your workloads and data.
Its advanced features and verified and enforced business policies help reduce risk by eliminating the attack surface.
Customer faults may lead to cloud security incidents. By implementing Cloud Security Posture Management, administrators can quickly identify misconfiguration issues and reduce such incidents.
Using this powerful tool, you can also secure app-to-web and app-to-app traffic and workload communications across different environments.
Who is it recommended for?
zScaler Cloud Protection is an excellent choice for businesses looking for a robust, scalable cloud security solution. Its features make it particularly useful for organizations that require deep inspection of their cloud workload communications and want to establish strong compliance management protocols. It’s also well-suited for administrators who need to remediate misconfigurations quickly to minimize business risk.
Pros:
- Easily secures all cloud data and workloads.
- Zscaler Cloud Protection helps reduce operational complexities
- Offers comprehensive protection to public cloud assets.
- Enables organizations to secure web/app traffic across cloud environments.
- Removes lateral threat movement within VPCs.
- Eliminates the need for hubs, full-mesh VPNs, and virtual firewalls.
- Provides proper compliance of cloud platforms.
- Remediates misconfigurations faster.
- Offers safe application access for only authorized users.
- Offers unparalleled flexibility and security to connect applications across environments.
- Allows use of advanced threat protection to inspect all transactions.
- Provides machine learning-driven policy recommendations automatically using Zscaler Workload Segmentation.
- It helps reduce data center resource consumption.
- Allows scanning the whole cloud system for quick threat detection.
Cons:
- By adding latency profiling network operations often turn difficult to manage.
zScaler Cloud Protection Pricing
Zscaler Cloud Protection platform supports different subscription models and is a bit expensive compared to Fortinet. Additionally, the cloud security platform requires an annual license to run the Zscaler Cloud protection platform. For more pricing details or licensing, contact and request the sales team.
Platform Support
zScaler Cloud Protection supports web-based devices and platforms.
Software Download Link
If your organization is looking for a cloud security platform that provides comprehensive protection to public cloud assets, download the product here.
Top zScaler Cloud Protection Alternatives
Clouds are one of the most convenient platforms for business computing but come with several security challenges. You cannot manage these challenges without a proper strategy and an effective security tool. One must look for various factors when selecting a cloud security system, such as if it covers hybrid systems, protects virtual servers, provides instant alerts, etc.
We have shortlisted some of the best cloud security tools available in the market and can be a great alternative to zScaler Cloud Protection. Check the below-listed cloud security tools and compare them before concluding.
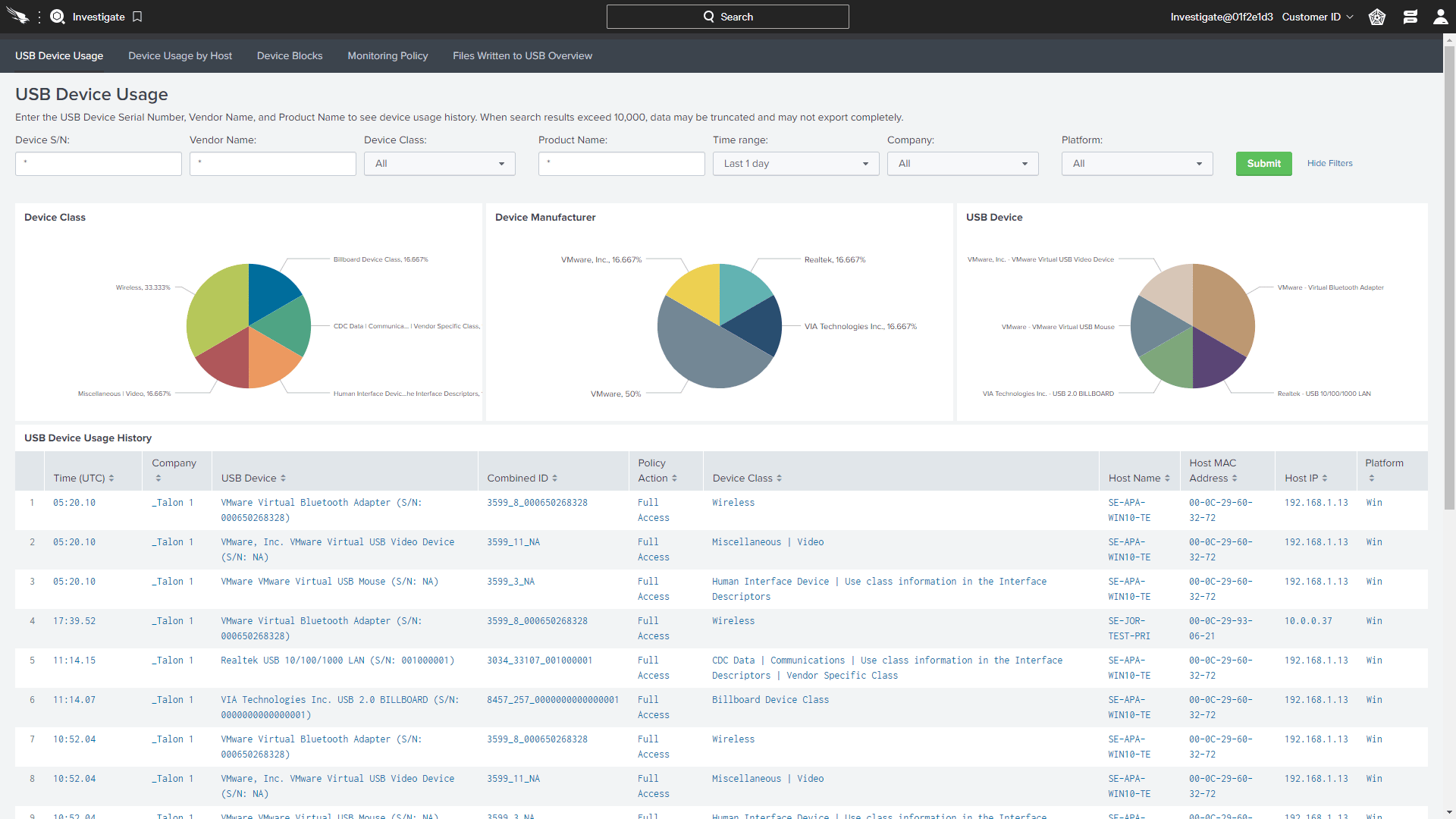
1. CrowdStrike Falcon Endpoint Protection
CrowdStrike Falcon Endpoint Protection is an automated security tool that protects and provides visibility into workload and container events. With the help of CrowdStrike Falcon Endpoint Protection, users can monitor the entire cloud estate from a single console enabling faster and more accurate threat detection.
Why do we recommend it?
We downloaded and installed CrowdStrike Falcon Endpoint Protection to test its claims of robust workload and container protection. Not only did the tool allow us to monitor our entire cloud estate from a single console, but it also excelled in quick threat detection, living up to its promise of helping users stay ahead of threats.
Cyberattacks can lead to heavy losses if you do not tighten your security. You can find many tools online for the same but what makes CrowdStrike Falcon Endpoint Protection stand out from the rest is its advanced features and ability to secure your entire cloud-native stack.
It helps you stay ahead of threats and eliminates the attack surface with its quick detection and monitoring capabilities. Another aspect of the powerful workload protection tool is it supports continuous integration/continuous delivery (CI/CD) workflows.
Using the latest techniques and technologies, businesses can further discover all the hidden threats, malware, or configuration issues. It also supports image scanning policies that enable organizations to keep a track of all their vulnerabilities, misconfigurations, and other security issues.
Get timely alerts and take the right action without rescanning images.
Who is it recommended for?
CrowdStrike Falcon Endpoint Protection is a versatile tool ideal for businesses that require a unified view of their cloud estate for real-time monitoring. It’s particularly beneficial for organizations adopting continuous integration/continuous delivery (CI/CD) workflows, as it seamlessly integrates into such environments. The platform is also highly recommended for security teams that need to act fast on timely alerts to block vulnerabilities before runtime.
Additionally, it grants you the authority to block all the exploitable vulnerabilities depending on IOAs before runtime. Thus, reducing the headaches often dealt with by the security teams.
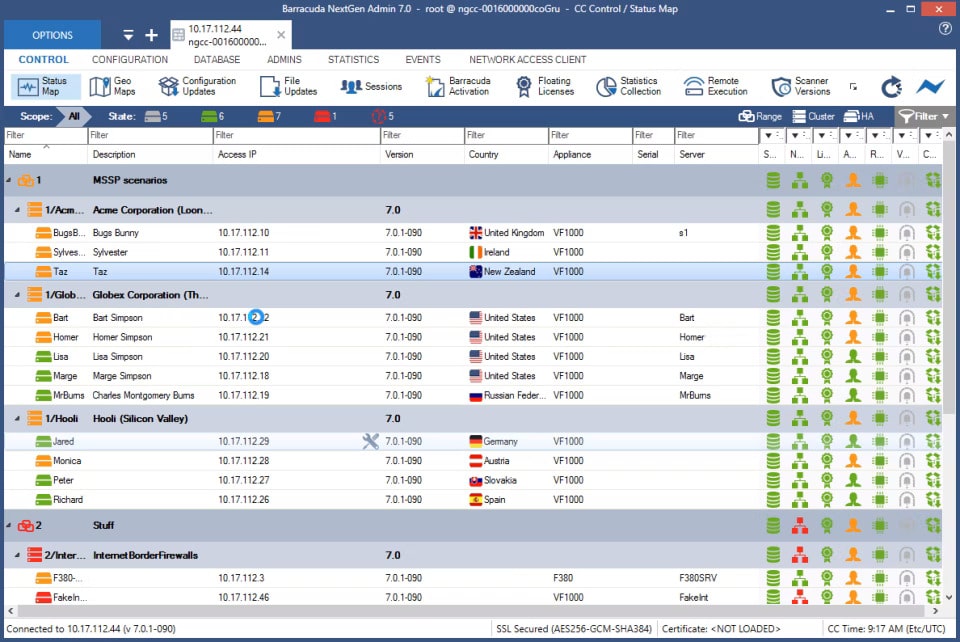
2. Barracuda CloudGen Firewall
Barracuda CloudGen Firewall is a cloud-based software that protects your dispersed network infrastructure with its multiple-layer detection system. Users can easily deploy Barracuda CloudGen Firewall on-premises or in the cloud using templates, APIs, and deep integration capabilities.
Why do we recommend it?
We took Barracuda CloudGen Firewall for a test drive in a sandbox environment to evaluate its multi-layer detection system and advanced threat protection. Our experience confirmed that it is efficient in real-time protection and seamlessly integrates into both on-premises and cloud infrastructures.
Also, for managing connectivity with distributed locations, you no longer need to purchase a separate SD-WAN.
Barracuda CloudGen Firewall is a great security tool that provides comprehensive protection to cloud and hybrid networks and supports various features that make it a better substitute for zScaler Cloud Protection.
Using its advanced threat protection services, your organization can also gain real-time protection from the latest threats. It helps collect threat data from different sources, identifies it, and shares the detail with all connected security solutions. These security systems push the information to the pre-filtering layers and immediately block the threat if it makes a second attempt.
Barracuda CloudGen Firewall supports the multi-layered security approach and strives to deliver better and more effective threat defense with its advanced threat protection service. Further, it helps mitigate cyber-risks by performing static code analysis, and behavioral and heuristic analysis.
Who is it recommended for?
Barracuda CloudGen Firewall is best suited for organizations with dispersed network infrastructures, looking for a single solution to manage both cloud and hybrid networks. If your organization prioritizes advanced threat protection and requires capabilities like static code analysis, and behavioral and heuristic analysis, this tool is an excellent choice. It’s also ideal for businesses that want to avoid purchasing a separate SD-WAN for managing connectivity across multiple locations.
If you want to protect your data, users, and workloads without compromising their performance, go for Barracuda CloudGen Firewall.
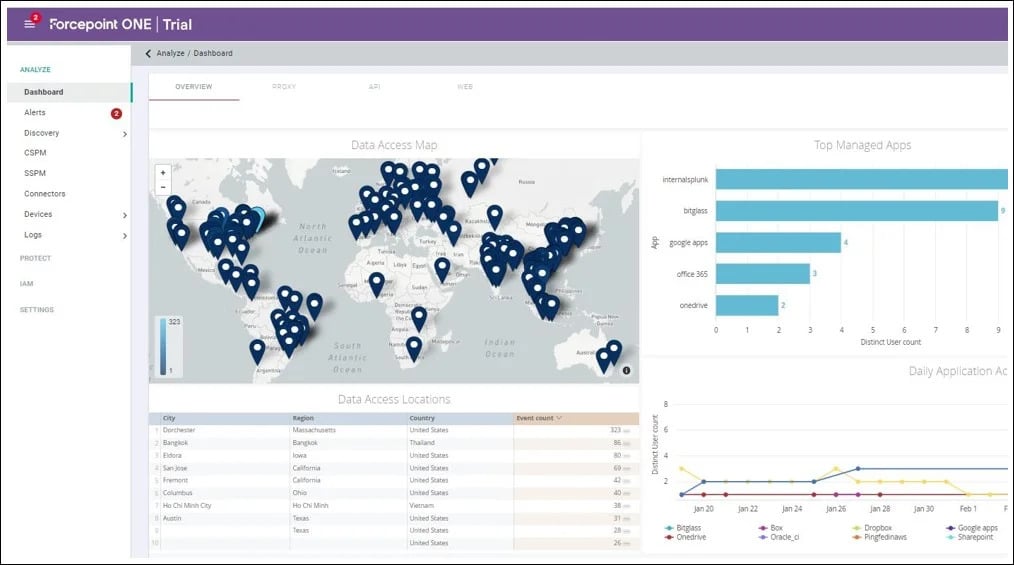
3. Forcepoint One
Forcepoint ONE provides comprehensive protection to your sensitive data stored on the web, in the cloud, or in private applications. It is an all-in-one cloud security solution that routes traffic locally and prevents data from malware and threats.
Why do we recommend it?
We installed Forcepoint ONE’s free trial to scrutinize its centralized cloud management and identity-based access control features. The platform proved to be user-friendly and highly efficient in routing traffic to prevent data from malware and threats, aligning well with its advertised capabilities.
Its centralized cloud management allows administrators to easily monitor and secure workload from any device. Forcepoint ONE is fully compatible with Windows and macOS devices and supports better integration features.
Gain more visibility into the collected data using its single console. It also offers identity-based access control that aids businesses in stopping hackers from getting in. It also supports a single set of login policies that prevent account takeovers.
No doubt, Forcepoint ONE is a great alternative to zScaler Cloud Protection. Using this popular tool and its excellent features, you can secure all your BYO devices, private applications, or web data from any location.
Further, it provides comprehensive reporting features that make it easier for teams to perform analysis and make better decisions.
Another plus point about the perfect tool is it allows organizations to monitor and control interaction with different platforms. Using its security policies, businesses can also protect all managed and unmanaged apps and devices easily.
Who is it recommended for?
Forcepoint ONE is a comprehensive solution well-suited for organizations that require strong data protection across a variety of platforms—web, cloud, and private applications. It is particularly useful for businesses with remote or hybrid workforces who need a single console for visibility and control. If you’re seeking advanced reporting features for analytics or need to secure a range of both managed and unmanaged apps and devices, Forcepoint ONE is a strong contender.
If you want to secure your remote and hybrid workforces, we recommend choosing Forcepoint ONE over other cloud security tools.
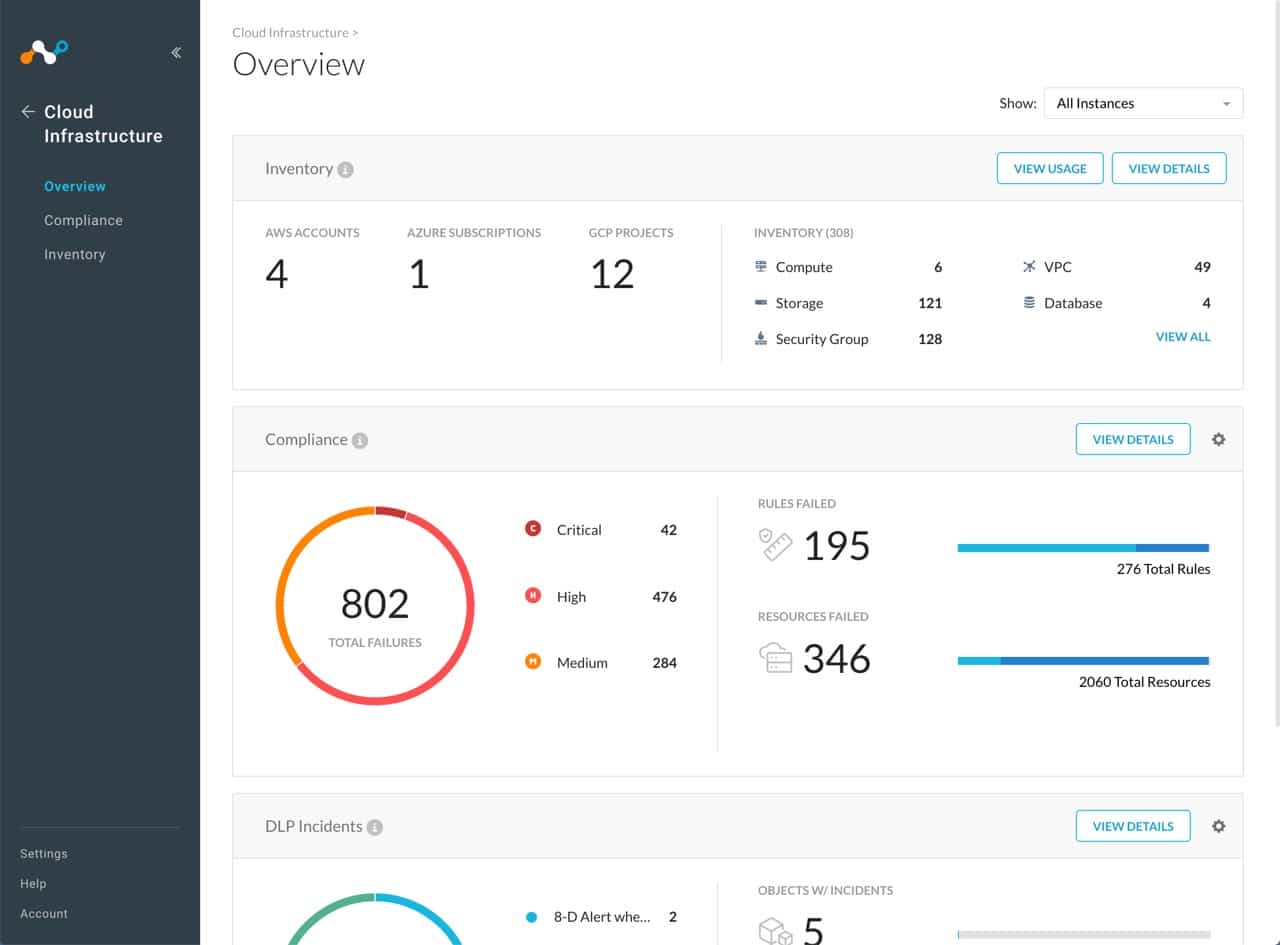
4. Netskope Public Cloud Security
When businesses move their workloads and sensitive data into public cloud infrastructure, they are also at a high risk of losing it all. The risk of exposure and certain cyber threats like malware are a few significant challenges that organizations must take care of and build a secure system.
Why do we recommend it?
After setting up Netskope Public Cloud Security in our sandbox environment, we were particularly struck by its Cloud Security Posture Management (CSPM) features and its ability to provide real-time threat defense. We also tested its misconfiguration detection capabilities and can verify that it efficiently identifies and remediate issues.
Netskope Public Cloud Security is a perfect solution for your public cloud security. It provides better visibility, compliance across your multi-cloud environment, and protection to sensitive data and critical workloads.
The cloud-based security tool helps in detecting misconfigurations and provides better security solutions against insider threats and malware. It comprises a wide range of security capabilities that make it a great choice.
Organizations can easily assess the security risks and manage the security posture with Cloud Security Posture Management (CSPM) features available for AWS, Azure, and Google cloud platforms.
It also allows businesses to scan their resources and provide better visibility into threats and DLP violations. Additionally, users have full access to capture DLP incident metadata in different locations as per their choice.
No doubt, many cloud security tools are available online, but Netskope Public Cloud Security is a top choice because it helps in monitoring and preventing network configuration changes from a single console.
Who is it recommended for?
Netskope Public Cloud Security is an excellent fit for businesses that operate in multi-cloud environments and are concerned with compliance and sensitive data protection. If your organization uses AWS, Azure, or Google Cloud and needs advanced capabilities like scanning resources for threats and DLP violations, this is a compelling option. The tool is also suitable for those requiring a unified view to monitor and prevent network configuration changes across different cloud platforms.
Further, the tool allows users to block malware moving to and from public cloud storage. It provides excellent threat defense in real-time and remediates issues faster.
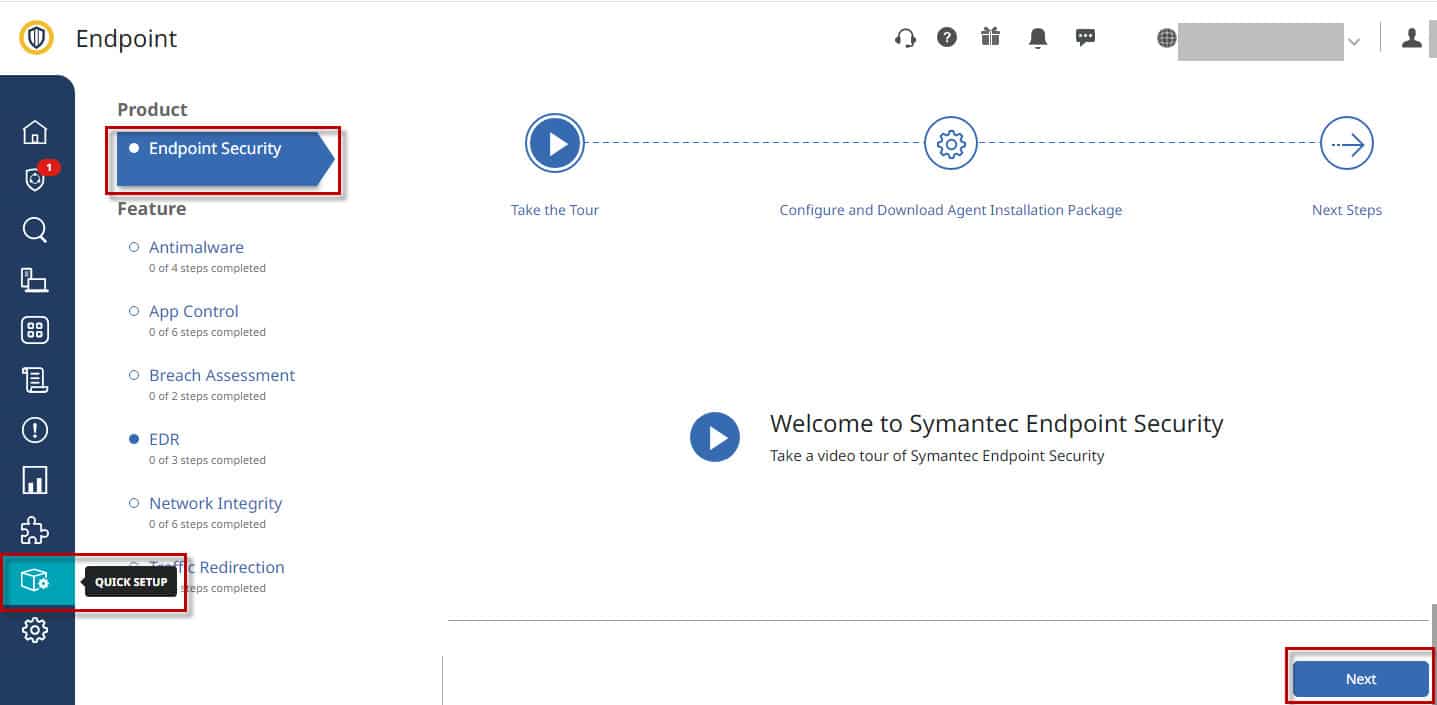
5. Broadcom Endpoint Security
Broadcom Endpoint Security is another great solution that stops threats and secures cloud workloads, containers, servers, and applications. With more and more use of cloud services, it is vital to look after the main line of defense. Endpoint security offers comprehensive protection and prevents attackers from compromising the environment or stealing the data.
Why do we recommend it?
We installed Broadcom Endpoint Security to rigorously test its capabilities in securing cloud workloads and containers. During our evaluation, the tool demonstrated swift threat detection and instant alerting on suspicious activities, substantiating its claims of comprehensive protection across all devices.
It uses innovative technologies to deliver unmatched protection, detection, and response across all devices. Further, its single cloud console architecture helps look after the overall endpoint security posture.
Using the Broadcom Endpoint Security solution, you can also monitor all the structured and unstructured sensitive content files, devices, and cloud storage spaces. It simplifies management and enables quick threat detection.
Another key aspect of the Broadcom Endpoint Security solution is it immediately alerts the administrators on discovering any suspicious activity or tracking an account. Also, it makes sure that only authorized users can access the sensitive data and that it remains encrypted at all times for better security.
Who is it recommended for?
Broadcom Endpoint Security is a well-rounded choice for organizations seeking endpoint security solutions that offer quick threat detection and robust protection for cloud workloads, servers, and applications. It’s particularly beneficial for administrators who need real-time alerts for suspicious activities and a single console for overseeing the overall endpoint security posture. The solution is also ideal for businesses that prioritize data encryption and require strict access controls for sensitive information.
If you want to prevent attacks and breaches or reduce the attack surface, look no further. Broadcom Endpoint Security is the perfect solution and delivers flexible deployment options.
Conclusion
With an increase in cybercrime, it has become essential for organizations to invest in cloud security tools that offer continuous monitoring and help eliminate threats in real-time from cloud workloads and containers.
To make it easier for you, we have shortlisted some of the best tools that can be highly advantageous for your cloud data and workload security. zScaler Cloud Protection is one of the trusted platforms to secure public cloud assets. Using its advanced features, you can quickly identify misconfiguration issues and reduce incidents.
We have also listed a few alternatives to zScaler Cloud Protection that can work in your favor and protect data against malware, ransomware, and other threats.
CrowdStrike Falcon Endpoint Protection, Barracuda CloudGen Firewall, Forcepoint ONE, Netskope Public Cloud Security, and Broadcom Endpoint Security are a few popular cloud security platforms that deliver similar features and great results.
Compare each above-listed cloud security platform before coming to any final conclusion. Look for the features, pros, and cons of the zScaler Cloud Protection solution, compare them with each alternative solution and their benefits, and then conclude.