Ransomware is one of the prominent malware threats that many online businesses face with outdated updates and fewer security tools. Over the past few years, the number of ransomware attacks has increased by 148%. As per the Business Insiders report, the largest ransomware payout was made by an insurance company in 2021.
Here is our list of the best tools to protect backups from ransomware:
- NinjaOne Backup – EDITOR’S CHOICE Offers customized, cloud-based, hybrid plans that give instant alerts when data is tampered with or misconfigured across the cloud platform. Start a 14-day free trial.
- ThreatLocker – FREE TRIAL An endpoint protection tool that prevents unauthorized applications, including ransomware, from getting installed on any device on your network, thereby protecting your network from these attacks. State a 30-day free trial.
- Acronis Cyber Protect – FREE TRIAL This package combines anti-virus with data backup and includes application-aware recovery for systems such as databases and VMs. Available for workstations, servers, mobile devices, and cloud platforms. Start a 30-day free trial.
- ManageEngine Ransomware Protection Plus – FREE TRIAL This is another comprehensive tool that can detect ransomware, neutralize it when possible, and protect your backups through features like device isolation and process kills. Start a 30-day free trial.
- ManageEngine RecoveryManager Plus – FREE TRIAL A robust enterprise solution for backing up and restoring data, ensuring seamless recovery when required. Its cloud-based storage shields your data from ransomware threats. Get a 30-day free trial.
- CrowdStrike Falcon Prevent Follows a modern approach by showing a malicious component in the detections dashboard to provide end-to-end visibility and protection.
Ransomware security is crucial for every small and big organization. With our prior experience and expertise, we have listed the top-notch security tools that can be a great addition to your organization.
These attackers give threat calls to victim companies of leaking exfiltrated data if their demands are not fulfilled. They cause not only financial damage to the company, but also ruin their reputation and brand value. Sophisticated cyber attackers know different ways through which they can enter your system. Once they gain access they infect and encrypt all computer files, and systems. Later, they demand a large ransom after activation.
Ransomware attacks can lead to both financial and data loss, and reputational damage. Here, we will discuss ransomware in detail and tips to help protect backup systems from such attacks. Furthermore, we have listed a few tools that can work in your favor and protect your business from ransomware attacks.
What is Ransomware?
Ransomware is a form of malware that blocks authorized users from accessing their computer files, systems, or networks and demands them to pay a ransom to unlock and decrypt the data. The attackers take advantage of software vulnerabilities to infect, access, lock, and encrypt the computer or device entirely, making it impossible for organizations to access any of its files or applications.
Ransomware is one of the most prominent types of malware that keeps all of your companies’ files and data hostage unless you fulfill their demand. It can infect any computer or mobile device connected to the internet, and commonly targets the one running outdated software. It is imperative you make sure your organization regularly updates its systems and apps to protect from such attacks in the future.
The reason why this type of ransomware is so dangerous is that once the cybercriminals get hold of your files, there is no way for security software or a system reset to retrieve them. If a ransom demand is not met in a cybercriminal’s timeframe, then your system or encrypted data remains unavailable. Also, your data can be deleted by ransomware, with its decryption keys being erased.
Cybercriminals can encrypt files on your system via email attachments, add extensions to your attacked data, and hold it hostage until you pay the requested ransom. Another technique that most attackers practice is to send notifications from malicious websites, informing users that their device is infected and must click on a download link to activate the tool and remove the virus.
The cybercriminal behind the attack will then contact you with their demands, promising to unlock your computer or decrypt your files after you have paid a ransom (usually in bitcoin).
Let us discuss a few tips that will help protect your backups from ransomware attacks.
Tips to Protect Backups from Ransomware
Do you know there are sophisticated ransomware packages that can be uploaded onto shared drives via syncing and travel across a network? These network-connected infections can also pass onto your backup systems and put the business into serious trouble. To avoid such mishaps and protect your backups from ransomware, we have listed a few tips that can work wonders for your business.
1. Secure Your Windows System
An uptick in remote work since the pandemic has seen ransomware attacks increase by 148%. It has also been found that most of these attacks are against Windows hosts and spread faster across other hosts after being infected by a single host.
In these cases, most of the attacker encrypts the files and devices once the infected ransomware spreads to enough hosts in your computing environment and shuts multiple systems altogether. Hence, the best tip for organizations would be to use other platforms for their backup server instead of Windows.
Unknown of the attacker’s possibility, many companies primarily use Windows to run their backup. As an alternative, you could switch to Linux media servers. However, if you want to still run the main backup software on Windows, try running a copy of your backup on Linux as well.
But if your backup is accessible only via Linux media servers, chances are that the ransomware attackers attempting to infect Windows-based servers will not be able to access your backup files.
Also, try to store the main backup behind a Linux-based media server to avoid any mishaps. Furthermore, work on the security of your Windows-based backup servers and turn off maximum services ransomware used to attack servers. Focus more on tightening your security and less on convenience.
2. Remove File-System Access to Backups
Avoid placing your backup data in a standard file-system directory. For example, E:\backups or C:\ProgramFiles. The attackers often target these directories with names to infect and encrypt files. You must always look for a different folder or destination to store backups on disk.
If you are using a backup server, try looking for new ways to write a backup product to your target deduplication array without server message block (SMB) or network file system (NFS). If the attacker can infect the server, it will encrypt all the stored backups as they are easily accessible via a directory.
3. Store Backups Out of Data Center
No matter which location you choose to store your backup data, make sure that its copy is stored in a different location. For example, in the case ransomware tries to attack your data center, your copies stored in the cloud must remain safe. Using firewall rules or changing operating systems and storage protocols, you can ensure your copies remain separate in the case of an attack.
Ransomware attackers indeed know different techniques to infect victims’ files but, they still don’t know how to attack backups stored in object-based storage. Further, there are a few backup services that can write backups to the storage but are not accessible except via their user interface. As a result, neither the administrator nor the ransomware can directly see the stored backups.
Use cloud platforms to store the backup copy and protect them by firewall rules or write it in different storage for security purposes.
4. Follow the 3-2-1-1-0 Golden Rule for Backups
The 3-2-1-1-0 Golden Rule is highly effective and provides the best protection from ransomware. As per this rule, you must meet five important conditions, including:
- Enterprises must create three data copies, including the production copy.
- Use at least two different storage media, such as tape and cloud storage.
- Out of the three, one copy must be stored off-site, in case the supporting machines are physically damaged.
- Out of the three, another copy must be stored offline or in the cloud (Immutable, i.e., it cannot be modified).
- The backups must have zero errors.
5. Automate Response
Another way to prevent contamination spread is to detect and respond immediately to the ransomware attack. In most cases, ransomware takes a minimum of 90+ days before activating and making a ransom demand. If your organization has a strong security posture, there are high chances that you can timely detect and prevent ransomware.
Various built-in monitoring systems can detect and alert your team to possible ransomware attacks. Also, integrate SIEM and SOAR platforms that help automate the response process.
Our methodology for selecting the best tools to protect backups from ransomware
You must follow this simple methodology to pick the right security tool to protect your organization from ransomware malware:
- Go through risk assessment according to your organization’s size.
- Consider implementing a comprehensive security strategy
- Look for features like anti-malware, anti-ransomware, and behavior-based analysis.
- Must have email and network security
- Regularly backup critical data in an isolated environment
- Consider a comprehensive incident response plan
- Consider tools compliance with relevant regulations and industry standards.
- Testing and evaluation
Tools to Protect Backups from Ransomware
Take a look at some of the trusted tools that will block and protect your backups from ransomware before they get inside your backup storage.
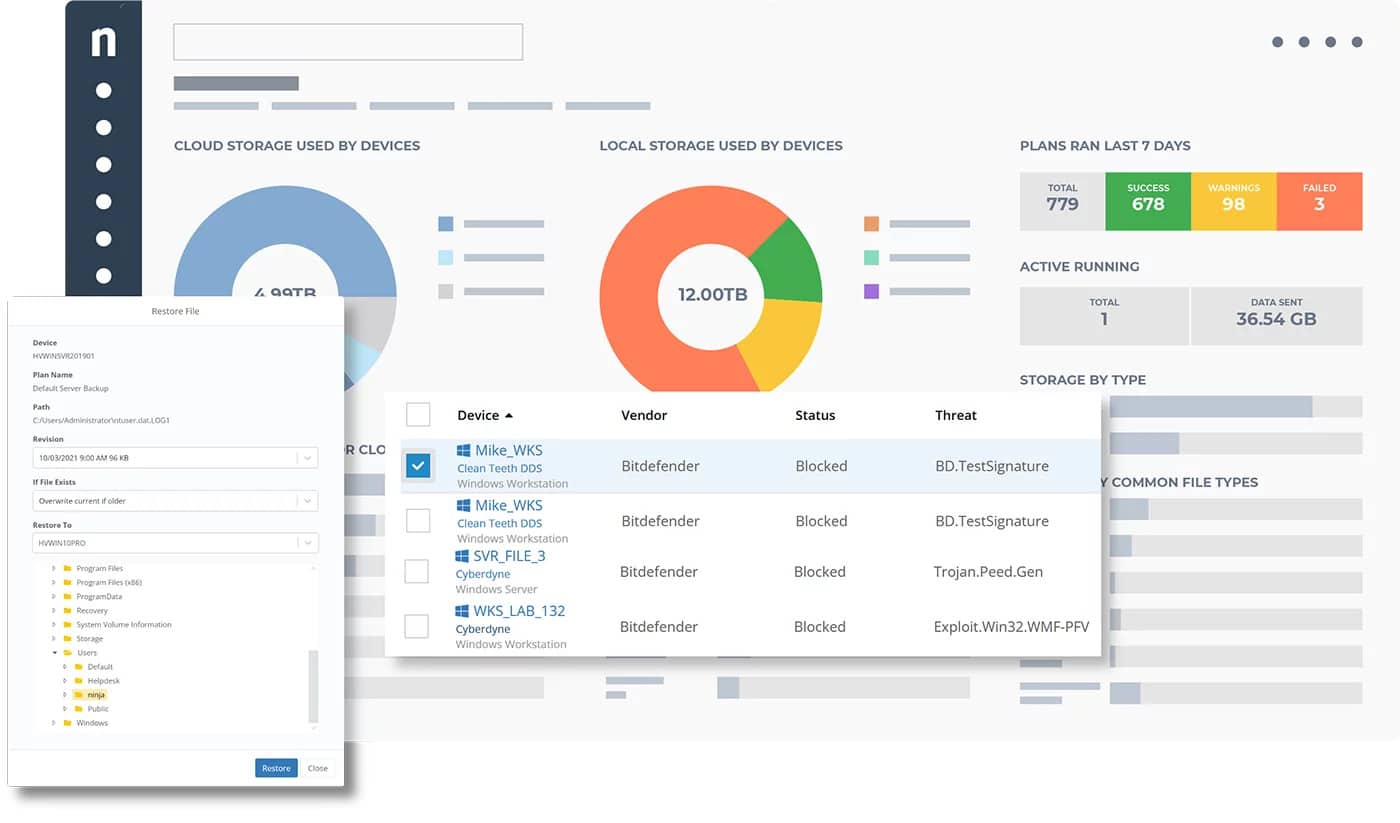
1. NinjaOne Backup – FREE TRIAL
NinjaOne Backup tool is best-suited for managed service providers (MSPs). It is a fast and flexible security tool that protects all your critical business information and data stored on end-user devices from known and unknown threats. It has a cloud storage space protected by 256-bit AES encryption that ensures all the data is safe from malicious actors.
Key Features:
- 360 degree control and visibility
- Bit defender integration
- Proactive alerting
- Remote backup management
Why do we recommend it?
NinjaOne Backup is well-known for its user-friendly features. It provides customizable file/folder and image backup plans along with multiple restore options. Other than this, it has plenty of great features like proactive alerting, remediation tools, and ransomware disaster recovery to ensure robust protection for all your endpoints.
Further, organizations can deploy data protection to the workflows and all Windows and Mac endpoints using this powerful tool. In case of a successful ransomware attack, the Ninja Data Protection tool helps faster restore all files stored locally or in the cloud to start operations.
Who is it recommended for?
Ninja Protect is recommended for cybersecurity experts seeking advanced threat protection. This tool is powered by Bitdefender’s next-gen antivirus and has HyberDetect machine-learning models and sandboxing capabilities. It helps experts by identifying suspicious attributes and behaviors to ensure effective and proactive defense against evolving cybersecurity threats.
Pros:
- Windows patching with granular management
- Allows to disable and hide new features
- It comes with various built-in tools
- MFA protection
Cons:
- Lacks extra integrations
You can inquire about custom pricing once you have registered for a 14-day free trial.
EDITOR'S CHOICE
NinjaOne sits at the top of our list for the best ransomware protection tool because it comes with extensive features to protect your environment from ransomware. It provides a 360-degree visibility into your endpoints and attack surface area and backs it with meaningful alerts. As a result, you can identify ransomware in its early stages and prevent the lateral spread of infection. Moreover, it automates backup and recovery to protect your critical business data.
Download: Start 14-day FREE Trial
Official Site: https://www.ninjaone.com/freetrialform/
OS: Cloud-based
2. ThreatLocker – FREE TRIAL
ThreatLocker has a unique feature called AllowListing, which allows only the authorized applications, executables, scripts, and libraries to run on a particular device. Besides giving complete control over what applications can be used on a device, it also prevents any malicious files from getting installed. This approach can safeguard your devices from ransomware attacks.
Key Features:
- Supports the addition of firewall-like policies.
- Enables administrators to allow applications for a specific time.
- Automatically adds hashes when new updates for existing applications are released, so administrators can make informed decisions.
- Restricts applications from accessing critical resources.
Why do we recommend it?
ThreatLocker is highly recommended because of its innovative approach to combating ransomware. Instead of the regular antivirus, which detects ransomware and sends notifications, this platform can proactively prevent these malicious files from installing in the first place. Additionally, applications can be prevented from itneracting with each other and accessing system resources, thereby adding another layer of security from ransomware.
Another feature is that it monitors the inbound traffic, making it easy to identify ransomware files before they enter your network. All these features can protect your devices and backups from ransomware.
Who is it recommended for?
It is recommended for large enterprises and MSPs who are responsible for maintaining a client’s environment. It can also work well for financial, healthcare, and other industries that have to follow strict compliance with multiple regulations.
Pros:
- Ringfencing that restricts application access.
- Role-based access controls for granular control.
- Monitoring of administrative privileges to prevent misuse.
- Zero-trust security that requires authentication before installation.
Cons:
- Requires the right configurations.
You can register for a 30-day free trial.
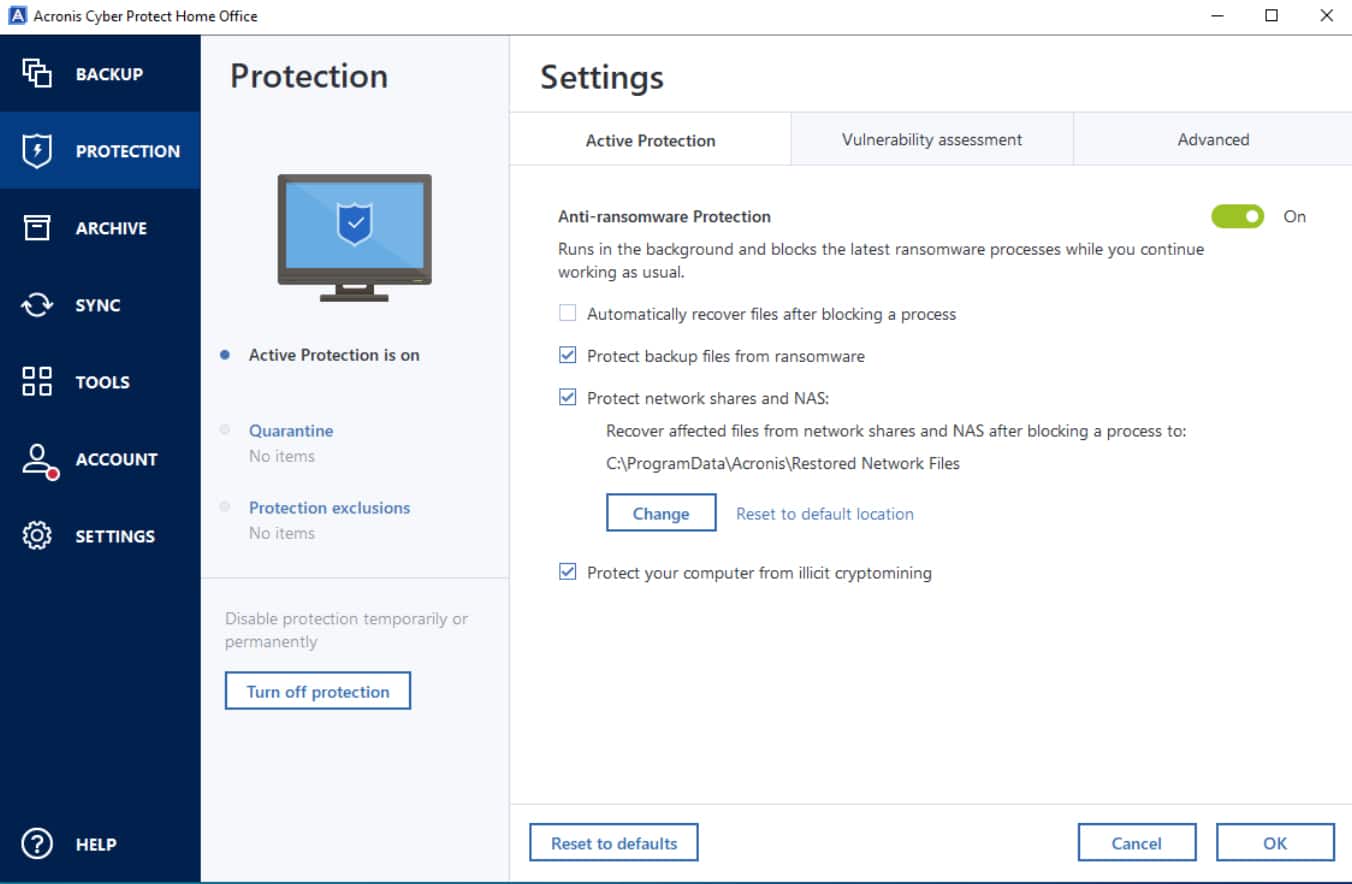
3. Acronis Cyber Protect – FREE TRIAL
Acronis Cyber Protect helps businesses manage, protect, and create a backup of multiple endpoints. It is a package of modules that safeguards your information and devices from threats and ransomware. It uses advanced MI-based protection against malware to protect every data and evolving threat.
Key Features:
- Active protection with foreign backup
- Anti-Malware and web protection
- Supports remote management and assistance
- Disk health monitoring
- Application-aware backup and recovery
Why do we recommend it?
Acronis Cyber Protect is the perfect security tool for advanced protection against ransomware. With its multi-layered security approach and AI assistance, it detects and mitigates ransomware attacks, keeping your data safe. You can always stay ahead of threats to ensure your organization’s security integrity and valuable information with this reliable backup solution.
Furthermore, it also supports various anti-ransomware technologies that help protect backup systems and eliminates the gap in the defenses. Organizations can easily scan all infections using its advanced features before getting added to the backup.
The backup restoration process also involves the use of malware scans. It is one of the best cyber protection solutions that offer a high level of efficiency and unmatched protection. Users can easily manage the tool and protect backup systems from ransomware via a single console.
Who is it recommended for?
Acronis Cyber Protect is ideal for IT experts who want a complete solution. It automatically finds new devices, making management easy. With built-in vulnerability assessments, experts can identify and fix weaknesses. The data protection map provides a clear picture of data activities, aiding strategic decision-making. It’s a must-have for efficient, secure data management.
Pros:
- AI-assisted threat detection
- Great GUI Backup
- Two-way data encryption
- Seamless cloud and local backup
- Customizable and faster recovery
Cons:
- Trouble in backup replication
Get started with a 30-day free trial.
4. ManageEngine Ransomware Protection Plus – FREE TRIAL
ManageEngine Ransomware Protection Plus is an AI-powered tool that uses advanced strategies like machine learning and behavioral analysis to quickly detect different types of ransomware. It even has the capabilities to neutralize a ransomware or sending an alert to administrators based on the configuration.
Key Features:
- Restores operations quickly to avoid downtime.
- Low impact on the system.
- Identifies ransomware that runs in memory and processes.
- Protects devices even when there’s no Internet.
- It isolates devices to prevent lateral spread.
Why do we recommend it?
Ransomware Protection Plus is a comprehensive tool that handles ransomware throughout its life cycle, from detection to recovery. It goes beyond just signatures, and uses techniques like behavioral analysis and machine learning algorithms to identify both known and unknown ransomware. Its continuous scans also detect fileless ransomware that runs in memory.
Once detected, it mitigates the impact by isolating infected devices. Depending on the configuration, it can automatically kill the associated ransomware processes or send notifications to administrators, so they can take quick action. To support their efforts, it helps identify the root cause of the problem and also, generates extensive reports for decision-making.
Due to such comprehensive features, we highly recommend this tool.
Who is it for?
ManageEngine Ransomware Protection Plus works well for organizations of all sizes. It is also a good choice for organizations that operate in regulated industries, like healthcare and insurance, as they deal with sensitive data.
Pros:
- Quick identification: Uses multiple strategies to quickly identify the presence of ransomware.
- Root cause analysis: Analyzes multiple parameters to identify the potential root cause.
- Proactive measures: It proactively scans devices for ransomware, and also, isolates infected devices to prevent their further spread.
- Recovery: Automatically connects with backup devices to restore data.
- Repeat offenders: Identifies software vulnerabilities that are conducive to ransomware and neutralizes their threat.
Cons:
- Complex: Wealth of features means it can be complex to set up for smaller organizations.
Start a 30-day free trial.
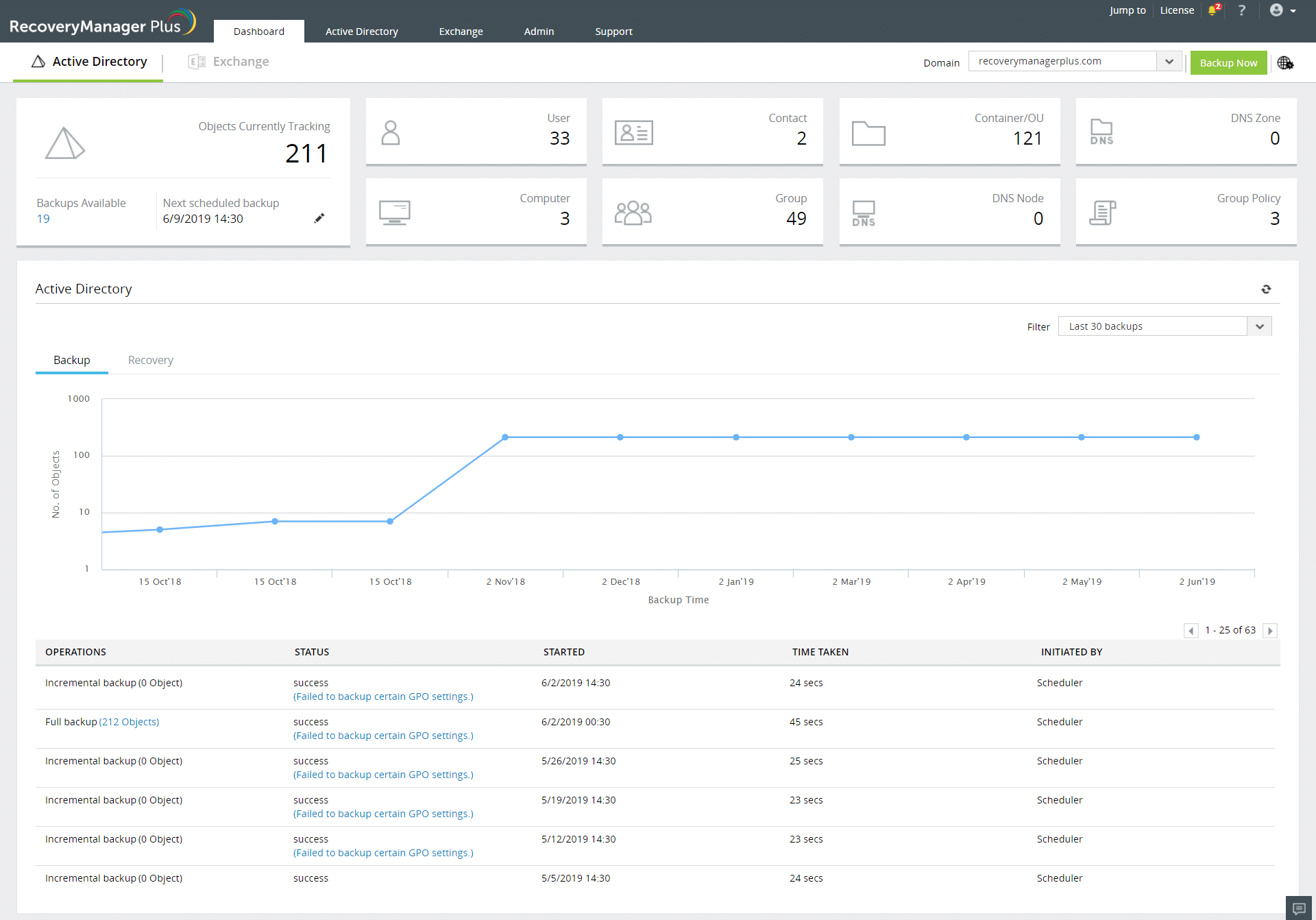
5. ManageEngine RecoveryManager Plus – FREE TRIAL
ManageEngine RecoveryManager Plus is a sophisticated enterprise tool designed for seamless data backup and restoration. It safeguards your data against cyber threats, including ransomware, and supports both full and incremental backups to keep your most recent data recoverable. It enables automated backup scheduling to streamline operations and reduce manual intervention.
Key Features:
- Supports granular restoration.
- Maintains multiple backup versions, depending on your retention configuration.
- Offers flexible configuration options.
- Safeguards data through role-based access controls.
- Centralizes backup and restoration through a single console.
Who do we recommend it?
We recommend RecoveryManager Plus because it is a hassle-free tool to store copies of your data for recovery and restoration. A highlight of this tool is its flexible configuration, where you can choose the type of backup you need, retention period, and the option to store data on the cloud or in local storage. These options enable you to customize your backup according to your internal policies and compliance requirements.
Based on your configuration, this tool automatically schedules the backup, requiring no human intervention. This seamless process minimizes errors and reduces downtime due to cyberattacks. More importantly, it can protect your data from ransomware attacks. Its centralized management console and option to work across environments are other reasons why we recommend it.
Who is it recommended for?
RecoveryManager Plus is a good choice for organizations that use Microsoft, Active Directory, and Google Workspace. It is also well-suited for medium to large organizations, especially those that have to meet the compliance requirements of different standards.
Pros:
- Secure storage: Enables you to securely store data in your local storage or on the cloud.
- Reduces downtime: Allows you to quickly restore the latest copy, reducing downtime.
- Supports compliance: Makes it easy to comply with different regulatory standards.
- Flexible configurations: Supports flexible policies.
Cons:
- Limited features: It does not go beyond backup and restoration.
RecoveryManager Plus has custom pricing based on the number of instances of each tool you use in your infrastructure. Start a 30-day free trial.
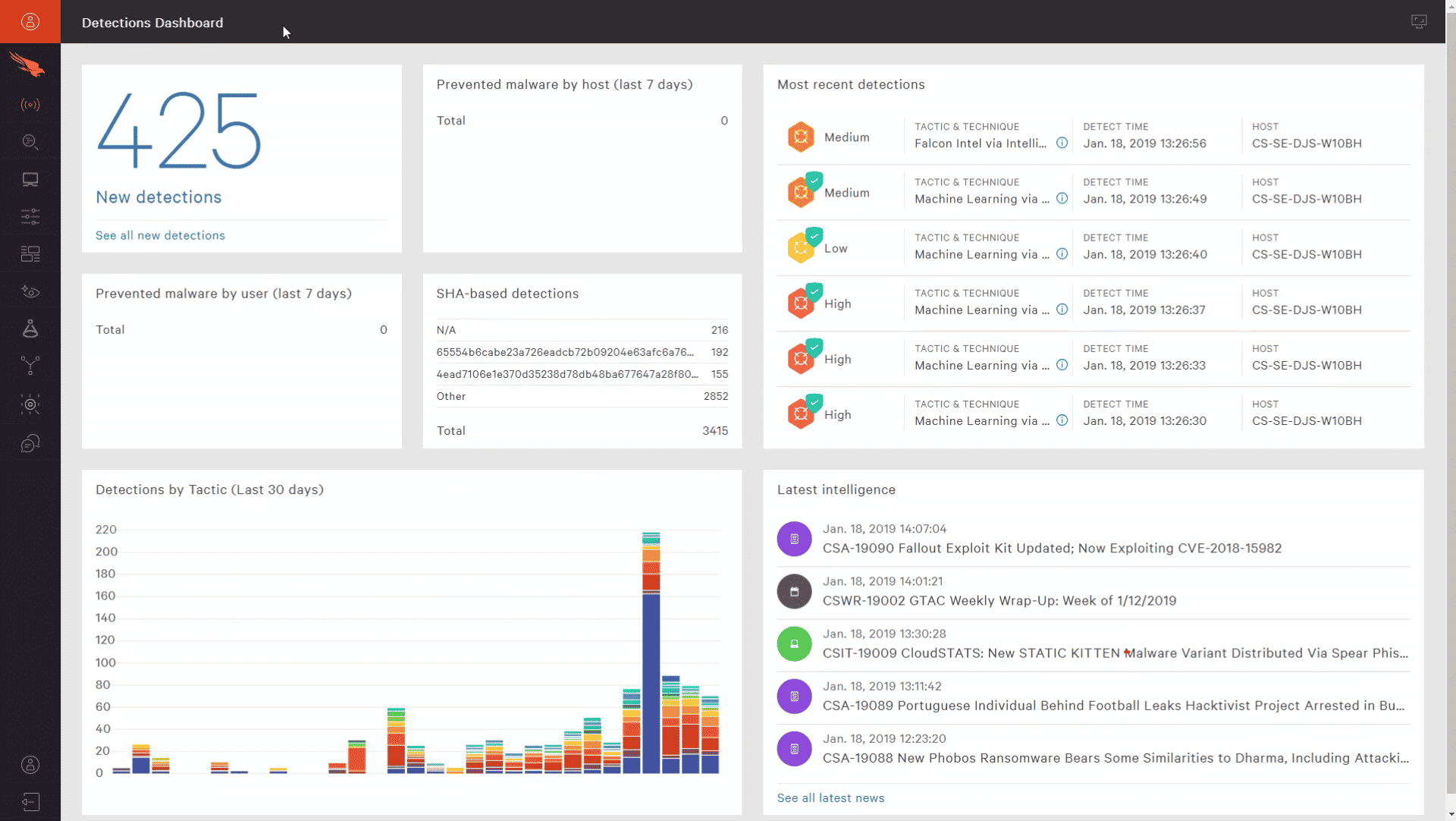
6. CrowdStrike Falcon Prevent
CrowdStrike Falcon Prevent is one of the best security tools available in the market to protect devices from ransomware infection. It is a fully operational tool that offers quick and easy deployment. Further, it protects your devices and backup files without impacting resources or productivity.
Key Features:
- Comprehensive application control
- Proactive threat hunting
- Gives rapid response
- Dynamic/code analysis
- Endpoint intelligence and malware detection
Why do we recommend it?
CrowdStrike is loved by professionals for its exceptional Endpoint Protection capabilities. It has advanced security measures, which reduces the time spent on manual issue remediation. In addition, it offers proactive defense to ensure overall cybersecurity posture and minimize potential risks to systems and data.
Falcon Prevent is an endpoint detection and response system that monitors each endpoint and detects and blocks ransomware as it hits the device. Its Automated IOA remediation feature further helps clean and eliminate artifacts left behind from blocked malicious activity.
It protects Windows, Windows Server, macOS, and Linux platforms and supports behavior-based indicators of attacks that go out of the way to prevent sophisticated malware-free attacks.
Who is it recommended for?
CrowdStrike is used by a broader range of cybersecurity experts and organizations seeking advanced threat protection. This tool helps in continuous monitoring of user behavior, which involves comparing real-time activity to benchmarked patterns and known fraud indicators. It helps in swift detection and response to anomalous activities, enhancing the overall security posture. Its proficiency in proactively identifying and mitigating potential threats makes it an invaluable tool for cybersecurity professionals tasked with safeguarding sensitive data and networks.
Pros:
- Supports End-Point Detection and Response (EDR)
- 24/7 threat hunting
- Regular follow and robust ability of detection
- Vulnerability management
Cons:
- Console menus are a little bit complex and unclear
Conclusion
Ransomware can get into your systems via mail attachments in PDF format, images, ZIP files, or RAR files. They can also make their way through your device by manipulating an employee or tricking them with fake information. Once the attackers make their way to your systems, they can access and encrypt all your files.
In some cases, they travel across a network and upload into shared drives to cause severe damage. Ransomware attackers are the main cause of concern for many online businesses as they can lead to financial loss, data loss, and reputational damage.
They can also infect your backup systems if not protected beforehand. Sophisticated ransomware attackers know different techniques to enter your space and infect files and systems. Therefore companies need to invest in the best cyber protection solutions that offer security to data, devices, and backup.
Make sure to secure your Windows system and store backup files in Linux media servers for better protection. Furthermore, avoid storing backup data in a standard file-system directory. Another way to protect your backup from ransomware is to store backups out of the data center in the cloud.
Lastly, follow the 3-2-1-1-0 Golden Rule and maintain a strong security posture to detect and prevent ransomware in real-time.
We have also listed a few security tools that will protect your backups from ransomware and block threats before they launch or cause any damage. Compare each above-listed security tool before selecting one for your backup and data protection.