Event log management is a crucial skill to acquire in all Windows systems. Every second, activity is recorded to Windows event logs, which serve as a security tool and a critical troubleshooting tool.
However, managing separate server event logs becomes unmanageable once a server setup develops past a few servers. Luckily, you have a tool called Windows Event Forwarding (WEF) to make things easier.
The event log forwarding in Windows Server allows system administrators to centralize client and server event logs, making it easier to monitor events without connecting to each server individually. The DMTF WS-Eventing standard is used for forwarding, part of the open Web Services-Management (WS-Man) protocol built into Windows Server as part of the framework.
Standards of Event Log messages
There are two major standards for log messages in use: Windows Events and Syslog. Syslog is a widely-used open standard on Linux systems. Windows Events adhere to a proprietary standard developed by Microsoft for its products. Third-party products, however, use the Windows Event log format when running on Windows. Similarly, some software developers choose to adhere to the Syslog messaging standard.
Framework for Windows Management (WMF)
In this article, we’ll walk you through configuring Event Log forwarding in Windows Server 2012 R2, including configuring a source server and a collector server. Windows Server 2008 and Vista or later are supported as event collectors.
Because Event Log forwarding uses technologies built into Windows Server, there is no need to install a collection agent. Forwarding is very scalable because one collector can forward to another and process many events per second. For secure messaging, HTTPS is also supported.
Log messages have recently grown in importance. Although every application and the operating system generates system status messages, system administrators have ignored them for decades. Everyone is now eager to collect and save every log message that every system emits.
- Collectors and receivers of logs The requirement to collect all log messages in one location necessitate the creation of a bridge between the two log messaging tribes: Windows Events and Syslog. A log message manager will collect and file all Windows Events log messages in a Windows system but ignore Syslog messages generated on other network parts. Similarly, a Linux log file manager would manage and store Syslog messages but not handle them.
- Messages from the Windows Event Log As a result, a systems administrator who manages both Windows and Linux systems must maintain at least two different log message stores – one for Windows Events and one for Syslog messages. This is an unfavorable scenario for intrusion detection. The solution to this problem requires either the conversion of Windows Event messages into Syslog format or converting Syslog messages into Windows Event message format. Either strategy would allow all system messages to be stored in standard files and searched using a single analytical tool. Converting Windows Events and Syslog messages into a neutral format is a third option for consolidating them. Event log forwarding refers to sending messages from Windows to a Syslog server or a third-party consolidating tool.
- Log servers and event log forwarders The Event log forwarder will only work on your system. The log server and consolidator are not required to be on your premises. There are log servers that can be installed on-site and others that are hosted.
- The Software as a Service (SaaS) model As part of the package, many hosted systems includes the log collector, also known as the Event log forwarder. In these cases, the log collector must still be installed on a Windows host on your site. This is commonly referred to as an “agent”. You will also need to install a Syslog forwarder on one of your Linux machines to combine files from Windows and Linux. A Linux-based agent is also available with SaaS log file management systems. If you host your log file server on your server, the log collector/forwarder and log server will remain separate packages. The server is designed to manage all log messages, whether Windows Events or Syslog.
What Is the Process of Event Log Forwarding?
As Event Log collectors, one or more devices can be configured. Subscriptions on these devices are configured to pull the desired logs from any source computer. There is no unique configuration required on the source computers, except that Windows Remote Management (WinRM) should be enabled, the WinRM Windows Firewall exceptions should be allowed, and the collector’s computer account must have read permission logs you want to subscribe.
This article does not cover variations on this standard configuration, such as configuring push notifications and configuring a user account to authenticate on the source computers. Additional configuration may be required if you work with computers in a workgroup rather than a domain.
What are the limitations of the WEC server?
Three factors limit WEC servers’ scalability. On commodity hardware, a stable WEC server should be able to handle an average of 3,000 events per second for all configured subscriptions.
- Disk I/O In WEC, the received event is not processed or validated. It is buffered and logged to the local event log file (EVTX). EVTX files can only be written at a limited speed due to disc write speed. WEC servers can receive more events per second if they isolate the EVTX files to their arrays or use high-speed discs.
- Network Connections While WEF sources do not maintain a permanent, persistent connection to the WEC server, they do not immediately disconnect after sending events. Therefore, the number of WEF sources connected to the WEC server simultaneously is limited by the number of TCP ports on the WEC server.
- Registry Size To store bookmark and source heartbeat information, a registry key (corresponding to the FQDN of the WEF Client) is created for each unique device that connects to a WEF subscription. If this isn’t pruned to remove inactive clients, this set of registry keys can quickly become unmanageable.
Monitoring event logs allow you to understand system metrics better, identify process bottlenecks, and detect security vulnerabilities. If you keep log data regularly, you most likely have a method for observing event logs in real-time, or you use batch processing. You can monitor event logs in two ways: manually and automatically. What are some of the other benefits of event log monitoring, and how can you make the most of it?
The Benefits of Event Log Management
All events can be in one place
While manual log monitoring can work well in a small environment, having an extensive network and system makes manually monitoring event logs exponentially more difficult. Log monitoring software allows you to keep track of local events and remote events in other parts of the network.
You can centralize event monitoring and control all logs in one place this way. You can customize how event logs are processed and parsed and which events trigger a response by creating a custom set of rules. One of the many benefits of centralized event log monitoring is increased security. In the event of a security breach on one machine, the intruder will be unable to access and compromise its event logs. They will have difficulty concealing their activities.
Improving performance system
Monitoring event log software archives all previous logs, providing an excellent data source for analyzing system behavior by storing all previous event logs in one location. For example, archived event logs can help you identify which processes waste resources or cause bottlenecks, improving resource management and performance.
You can detect minor problems by monitoring event logs in real-time, and you can prevent further problems before they cause further problems that could cause more severe problems. Because you can customize how you perform event log monitoring, you can develop a method that works for your infrastructure and filters out less significant events to focus on the important ones.
Time-saving
Monitoring event logs typically involves manual monitoring and acting when an issue is detected. The disadvantage of this approach is that someone must constantly monitor event logs, which necessitates more people working in shifts or forces you only partially to monitor the system during specific working hours. Suppose a critical issue arises outside of working hours and you do not have a dedicated person to handle emergencies. In that case, this can result in hours of downtime before someone is available to address the issue. Such events may result in an increase in customer churn, which you should avoid at all costs.
Using Software to monitor log events can avoid this problem and reduce the time required to detect and resolve an issue. Event logs can become large and difficult to navigate manually, which is another reason to automate and speed up the process. Suppose you believe that time is of the essence when a security breach occurs. In that case, automated monitoring can assist you in reacting in real-time by sending real-time alerts as soon as a security issue arises.
One of the most valuable features of automated event log monitoring is configuring the monitoring software to act automatically whenever a specific type of warning is detected.
Automatically fix issues
Another significant advantage of using automated log monitoring is configuring the monitoring software to take action when a specific event occurs. There is a universal and straightforward solution for some events every time the event occurs. This reduces the time required to detect the event and decide on the best course of action and ensures system uptime without human involvement. Some events, for example, generate a low memory warning, which can be resolved by restarting the complex process or the entire system. Configuring an automatic action, such as resuming a function every time it triggers a low memory warning, can save a significant amount of time between detecting a sign in the event log and resolving the issue.
Commercial Event Log Forwarding Software
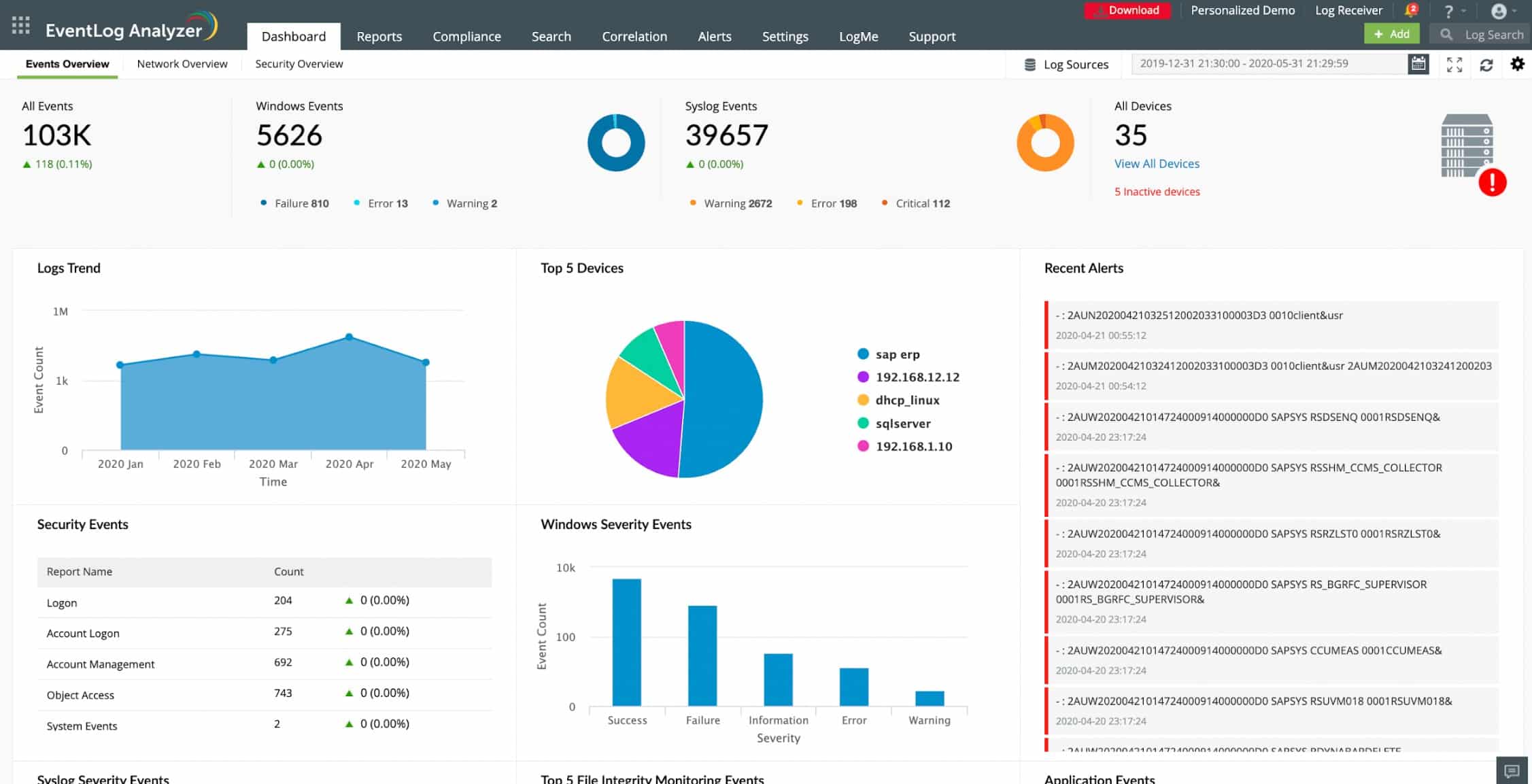
The Event Log forwarding function is built into many log management packages. One example is ManageEngine EventLog Analyzer. This package acts as a log server, receiving logs from multiple sources and in different formats. It is able to collect Windows Events and Syslog as well as many application-specific log formats. The service will convert all of the logs it receives into its own standard format. This enables it to forward logs from different sources to different destinations.
The package allows administrators to set up a custom format for each log before sending it on. All log messages can be displayed together in one stream, which enables log correlation and security or performance scanning. Users can set up their own queries to run continuously. This creates a customized performance monitor or security scanner.
The EventLog Analyzer system is an on-premises package and it will run on Windows Server or Linux. You can examine the system and try out setting up your own parsing or format conversion routines by accessing a 30-day free trial.
Inside the Perimeter Security
Security is always at the forefront of any organization’s IT strategy, regardless of size. Typically, this strategy focuses on the network’s perimeter to prevent unauthorized access or attacks from malicious parties unaffiliated with the organization.
As discussed in the Executive Summary, the potential for liability is significant when an unauthorized individual gains access to data protected by legislation. A security breach is just as likely to occur from within the organization as it is from without. It could be even higher.
You can locate and prevent small events before they turn into significant disasters by establishing a comprehensive ELM strategy for security monitoring of Windows event logs for internal activities and changes outside the scope of normal business activities.
Prepare for the Worst in Compliance Initiatives
Regulatory compliance may or may not apply to your organization. Most likely, if you are a private entity, you do not. However, this should not prevent you from comprehending the requirements of the regulatory standards. Using these standards as a guideline can provide you with a framework for your internal security plans and log management strategy.
Many of the requirements for log management in other legislative or industry-specific initiatives for security and compliance overlap with those of Sarbanes-Oxley. Non-compliance with Sarbanes-Oxley, for example, can result in heavy fines and legal liability for the officers if your organization is public. As a result, every public company and many private companies look to that standard for guidance when developing a log management strategy.
A high-level overview of each of the standards listed below will provide you with a comprehensive understanding of how they can affect your log management strategy.
The decision to implement event log monitoring is entirely up to you. Still, the benefits far outweigh the costs of time and human resources (if manual monitoring is chosen) or money (if you choose paid event log monitoring software). If you decide to use event log monitoring software, compare different products and features before making a final decision.