With the rise in remote work and companies moving to digital platforms, we are also noticing a surge in cyberattacks. More and more companies are moving to digital platforms, they are in a way putting their sensitive data at risk.
However, some practices can reduce the impact and prevent attackers from accessing the crucial data. But, if you lack proper optimization of your security environments, these cyberattacks or threats can result in operational losses and harm your goodwill.
To identify and remediate vulnerabilities, you can find several powerful tools online. One of them is Detectify, introduced around 2013 by Detectify Crowdsource.
Here, we will discuss Detectify in detail, highlighting the different deployment options, pricing plans, features, pros, and cons. Further, we will discuss a few alternatives to Detectify that can also be beneficial for your business.
Detectify Product Overview
Detectify is an automated vulnerability scanner that provides full coverage to the growing attack surface or threat. Thousands of companies worldwide trust and use Detectify to discover security vulnerabilities.
Key Features
- Asset Discovery
- Vulnerability Assessment
- Web Scanning
- Up-to-date vulnerability scans
- API
- Application Security
- Access Controls/Permissions
- Endpoint Protection
- Real-Time Analytics
- Real-Time Monitoring and Reporting
- SQL Injections
- Third-Party Integrations with tools, such as JIRA, Slack and Zapier
- Two-Factor Authentication
- Single Sign-On
- SSL Security
- Website Crawling
- Protects attack surface
- Develops secure apps
- Report exports
- Runs customized scans
- Role-Based Permissions
- Supports 2000+ security tests
Why do we recommend it?
Detectify offers a comprehensive set of features for vulnerability assessment, ranging from real-time analytics to third-party integrations. Its automated scans are constantly updated to detect new threats, making it a reliable tool for businesses serious about cybersecurity.
The team keeps you ranked on top of the threat with its excellent services and advanced features. Using Detectify, businesses can scan their system daily, remediate vulnerabilities faster, and improve discovered assets.
Many high-profile companies, such as Trustly, Spotify, Grammarly, SMART BEAR, etc., trust Detectify for automated discovery and quick remediation features. In fact, with the help of Detectify, users can keep an eye on various Internet-facing assets and perform regular scanning to discover vulnerabilities and misconfigurations in real-time.
Further, the application provides timely alerts on detecting vulnerabilities and advice on how to fix the issues.
Detectify is one of the best systems to register and report security weaknesses. It supports an open-source security research mechanism and includes no upfront costs for running the team. The penetration testers are paid only in case they discover a new exploit.
Most cybersecurity companies invest money in discovering product-specific weaknesses, but it all goes to waste because as the problem is detected, a patch is issued for the same, and weaknesses get eliminated. The operating research labs provide free system testing services to all software producers.
Here, Detectify comes into the picture and acts as a middleman. The platform has put an end to the high cost of research and introduced individual technicians to manage the risk of never recovering research costs.
Who is it recommended for?
Detectify is ideal for businesses of all sizes that have a broad attack surface and require constant monitoring for vulnerabilities. Companies in high-stakes industries like finance and technology, which cannot afford any security lapses, would particularly benefit from its real-time alerts and remediation features. The tool is also well-suited for organizations that leverage multiple third-party tools, as it offers seamless integration options.
Pros:
- Cost-effective solution compared to other CI/CD testing services or vulnerability scanners available in the market.
- All you require is to insert the asset address into the dashboard to use the service easily.
- No additional cost is to be paid for software maintenance as it is all included in the price.
- Choose internal and external scanning strategies as per your requirement
- Offers full coverage to the attack surface
- Regular scanning of development, staging, and production environments with quick remediation of vulnerabilities
- Allows monitoring large Internet-facing assets
- Discovers misconfigurations and vulnerabilities
- Supports excellent security defenders
- Protect attack surface
- Checks code for vulnerabilities and helps develop secure apps
- Supports report-sharing features
- Users can check for 2000+ vulnerabilities in a web application.
- Supports third-party integrations
Cons:
- The exploit detection strategy offered by Detectify Crowdsource is less effective.
- Auto-detection for frameworks like WordPress, Magento, etc., is not supported.
- Information related to API changes is not passed to customers in some cases.
- Visibility and user privilege setup is less flexible.
- The overview feature for administrators is not available, which makes it difficult for large organizations to manage teams.
- Difficulty in changing subdomains when scanning.
Detectify Pricing Plans
There are three pricing plans available for users, including Deep Scan, Asset Monitoring, and Get it all. The Deep Scan plan covers all the scanning within the organization. The second one, i.e., asset monitoring, is an external vulnerability scanner. And, the last one is a combination of Deep Scan and Asset Monitoring. The Get it All plan also includes bespoke system security advice.
Even if users take a subscription to both plans (Deep scan and Asset monitoring), it can’t replace or cover the Get it all plan features because it provides additional features such as consultancy services.
Deep Scan
Most DevOps choose the Deep Scan plan as it is suitable for integration into a CI/CD pipeline. Under this plan, DevOps are provided with scheduled, regular, and on-demand scanning options. Users can choose between the autodiscovery process or on-demand scanning as per their requirements.
Further, you can upload a list of assets from different sources like AWS Route 53 or Google Analytics and run scans for the same. The generated report highlights all weaknesses found in the list of assets and proper guidance to fix the issue. It also supports the concept of testing input options and application reactions.
The Detectify Crowdsource system constantly updates discoveries to the Deep Scan knowledge base. The main benefit of the Deep Scan system is it supports third-party integrations with tools like Splunk, Jira, Slack, Trello, Webhooks, etc. All these features provided in the pricing plan make automating test launches easy.
The Deep scan plan ranges around $85 per month on annual billing.
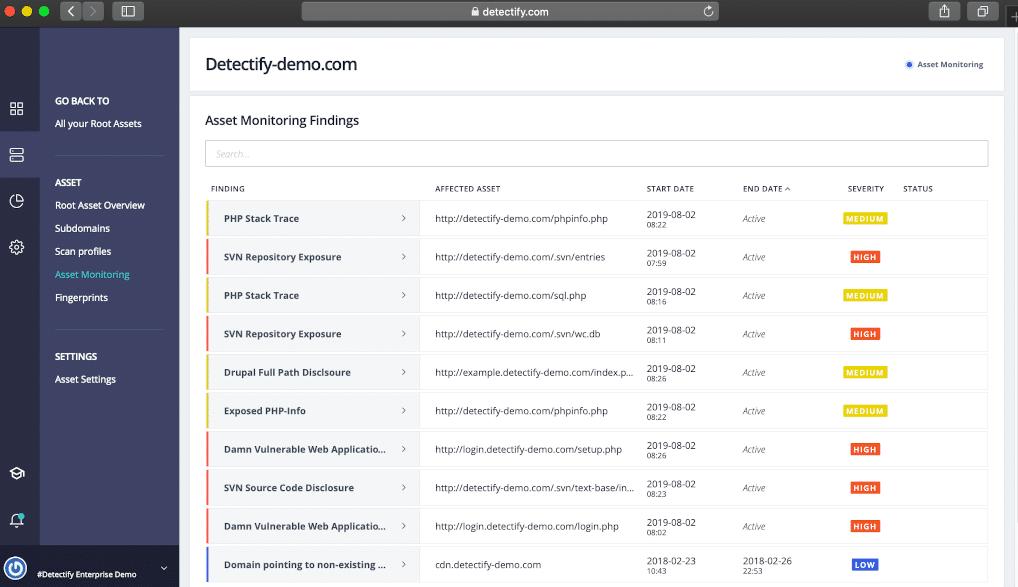
Asset Monitoring
Detectify Asset Monitoring does not support dynamic testing strategies. Under this pricing plan, users perform external scans and practice DAST method to discover vulnerabilities.
If you are looking forward to taking Asset Monitoring, let us tell you that the service is run from the Detectify SaaS platform’s dashboard. A URL is inserted in the dashboard, and the automatic scanning feature is turned on.
The manager will start noting all the components visible on the pages of the provided website. Later, it checks and scans the location of each service. The process continues to run unless all the supporting infrastructure is traced by the tool.
The scanning process covers DNS records, containers, and container management systems.
It can also be integrated with other project management tools, like Jira and Slack. Later, it also provides recommendations for fixing the identified issues.
The Asset Monitoring plan ranges around $420 per month on annual billing.
Detectify Deployment Options
Detectify is available to users only as a SaaS platform, i.e., the service can be accessed only using a dashboard hosted on the Detectify server. Also, all the processing functions are run through the dashboard.
Additionally, you can install free plugins and run third-party integrations with apps like Jira, Splunk, etc.
Best Detectify Alternatives
Detectify provides full coverage to attack surfaces and information about security weaknesses. No doubt it is hard to beat Detectify’s unique methods and features, but there are multiple alternatives you can choose from matching your business requirements.
- ManageEngine Vulnerability Manager Plus – EDITOR’S CHOICE This software package for Windows Server is able to scan endpoints running Windows, macOS, or Linux and it includes a patch manager. The system scans for configuration weaknesses and, in some cases, can automatically correct those loopholes. However, in most cases, the scanner will produce a to-do list that details which errors need to be corrected on which endpoints and how to do it. Among the risks that the tool searches for are weak account security, the presence of unauthorized communication utilities, RDP without credential requirements, and lack of password protection of the screen lock and system utilities. The package also provides Web application security, such as HTTP misconfiguration scanning, DNS and SSL certificate checks, and susceptibility to directory traversal and cross-site scripting. Start a 30-day free trial.
- Invicti An automated application security testing platform used by DevOps for testing CI/CD pipelines and other IT operations. It has a vulnerability scanner that helps discover SQL Injection, Cross-Site Scripting (XSS), and other forms of threats. At times a few vulnerabilities are not counted as errors in competitor testing systems, but with the help of Invicti, no vulnerability is left unnoticed. Even a minor vulnerability can compromise a system. Hence, it is best to invest in a tool that automates security throughout SDLC and provides real-time monitoring services. Using the dynamic + interactive (DAST+IAST) scanning approach, you can easily identify real and false vulnerabilities and achieve effective results.
- Acunetix A vulnerability scanner that helps pinpoint network weaknesses and enables businesses to scan all vulnerabilities. The external vulnerability scanner of the tool allows searching for 7000+ exploits, and the internal scanner supports searching for 50,000 network-based exploits. It is commonly used by enterprises for scanning IT operations and DevOps testing. Acunetix helps discover security threats in real-time and supports platforms like Windows, macOS, and Linux. If you are planning to switch Detectify, go for Acunetix, as it helps eliminate false positives automatically. Further, you can Schedule scans, prioritize high-risk vulnerabilities, and perform audits on all complex applications with the help of this powerful tool.
- SpectralOps Another trusted cybersecurity software that helps businesses in monitoring and protecting codes, assets, and infrastructure. Many high-profile brands and companies, such as Similar Web, Moonshot, Wobi, Kryon, etc., trust SpectralOps. The platform ensures that all your stacks and assets stay secure and free from the risk of attacks. The tool helps monitor public blindspots, automate the processes, and enables users to detect API keys, tokens, security misconfigurations, and more. Another key feature of SpectralOps is that it can seamlessly integrate with playbooks and implement mitigation policies as per the requirement. The main purpose of designing SpectralOps was to protect your systems against harmful security errors in code and detect vulnerabilities faster.
- Orca Security One of the most comprehensive agentless cloud security platforms that helps identify and prioritize cloud security risks in less time. Comparing other vulnerability scanners, it is one of the best tools in the market that protects your workloads and manages infrastructure entitlements. Further, it provides full coverage and compliance for Amazon Web Services, Azure, and Google Cloud platforms. One can detect malware, misconfigurations, vulnerabilities, and other issues easily with the help of Orca Security. Later, you can also prioritize the risk depending on the environmental context. If you are looking for a platform that provides multiple tools, full visibility, and 100% security, go for Orca Security.
- AppTrana Indusface AppTrana is another web application firewall that also provides scanning and risk-based protection. The platform makes it easier for businesses to manage and maintain cloud security. If you want to monitor your traffic, perform penetration testing, detect risk or always maintain security, go for Indusface AppTrana. The customized dashboard of the platform provides users a 360-degree view of their application security, timely updates, and notifications on detecting threats, and helps create amazing visual reports. Using automated security scans and manual Pen Testing, businesses can continuously monitor risks, bandwidth usage, the total number of attacks, etc. It also supports vulnerability patching and DDoS monitoring.
Conclusion
Cyberattacks are increasing day by day. The only solution to protect your business from operational losses is to implement tools that provide full visibility into your system, detect threats before they launch, and provide endpoint protection.
Detectify is one such popular automated vulnerability scanner trusted by most DevOps for CI/CD testing services and IT operations security. It is also one of the cost-effective methods businesses use to scan their system daily and improve discovered assets.
Today, many high-profile companies, such as Trustly, Spotify, Grammarly, etc., are using Detectify for automated discovery and to remediate vulnerabilities faster. It also provides timely alerts to businesses on detecting vulnerabilities before they launch.
Asset Discovery, Vulnerability Assessment, Web Scanning, Real-Time Monitoring, and Reporting are a few key features of Detectify. There are many reasons to invest in this platform for detecting vulnerabilities and saving your system from high risk.
However, the tool also has a few drawbacks which is why people look for alternatives, such as the exploit detection strategy being less effective, expensive for small enterprises, etc.
We have also highlighted the pricing plan and deployment options for the tool to make it easier for you to decide. If for any reason you want to switch from Detectify and look for similar software, check out the alternate section.
We have listed a few alternatives to Detectify that also provide automated vulnerability scanning and help businesses pinpoint network weaknesses.
ManageEngine, Invicti, Acunetix, SpectralOps, Orca Security, and Indusface AppTrana are a few popular platforms that provide full coverage and manage infrastructure entitlements.
Compare the above-listed tools, look for their pros and cons, and then make a call for your business security.