Email is the most popular and preferred channel for business communication today. It is estimated that about 63% of business professionals prefer to use emails for their business communication, and each employee sends an average of 40 emails per day for business purposes.
But there’s also a downside to this widespread usage, and that’s unauthorized viewing or hacking. Emails use an open format and don’t have any built-in security. This is why anyone who wants to send malware, ransomware, or a virus uses email as a vector for their nefarious activities.
Now comes the big question – what can you do to protect your emails?
A robust email security policy implemented using top-notch email security software and supplemented by security best practices can greatly bring down the chances of attacks. In this article, we will focus on the business email best security practices that you can implement within your organization.
Use a Strong Password
When a hacker knows a password, he or she can take over the account, and use it to send malware and ransomware to unsuspecting victims. Since the source is from a legitimate account, many security systems may not flag it, and users will also implicitly trust the email contents.
To prevent this situation, every user must have a strong password that is hard to guess. Passwords like “123456” or “abcdef” are the most common and can be guessed by anyone. It’s best to have an organization-wide password policy to ensure there are no weak links in your network.
Your password policy should include the following.
- A minimum of 12 characters
- A random combination of lowercase, uppercase, numbers, and symbols
- Unique and must not have the user’s name, date of birth, or any other personal information
- No common phrases and no proper sentences
- Must not be used anywhere else
While these rules are not written in stone, they sure give an idea of how to enforce a strong password policy across your organization.
Implement Multi-Factor Authentication
Multi-Factor Authentication (MFA) offers another layer of security for your passwords. Often, you will be asked to enter a code sent to your registered phone number by SMS or voice calls, to access your email account. Many email service providers also use authenticator apps for the same.
MFA is a safer option because even if a hacker manages to crack your password, he or she will not have access to the secret code sent to your phone.
Regular Training
Even the best email security policies are not effective if they are not followed by your employees. This is why it’s important to provide regular training sessions for employees to help them understand the need for email security. Explain the different types of attacks such as phishing and whaling and the potential impact of the same on the organization.
Teach them to identify malicious malware and ransomware emails, and encourage them to reach out to the IT help desk if they are unsure of an email’s safety. More importantly, ask them never to click on any link in the email that can potentially take them to a malicious site.
Use an Email Security Software
Many times, hackers send viruses as attachments in an email and you’d not want them to even enter your network in the first place. Email security software does exactly this for you.
It scans the header and contents of an email and stops any malicious email from entering your system. Further, it sends notifications about the blocked email, so you know how an attack was averted. Many tools use a multilayered approach to detecting malicious emails and you can even provide custom rules such as blocking emails from an IP range, location, etc.
Although spam is an inconvenience instead of a security risk, many spam filters also provide security scanning of content as well. For example, phishing is a little more threatening than the spam strategy of mass advertising by email. With a phishing attempt, hackers link through to fake log in screens for well known sites, including online banking and streaming services. Users who enter their credentials into those screens are giving their accounts to hackers. This method is also used for access to corporate accounts.
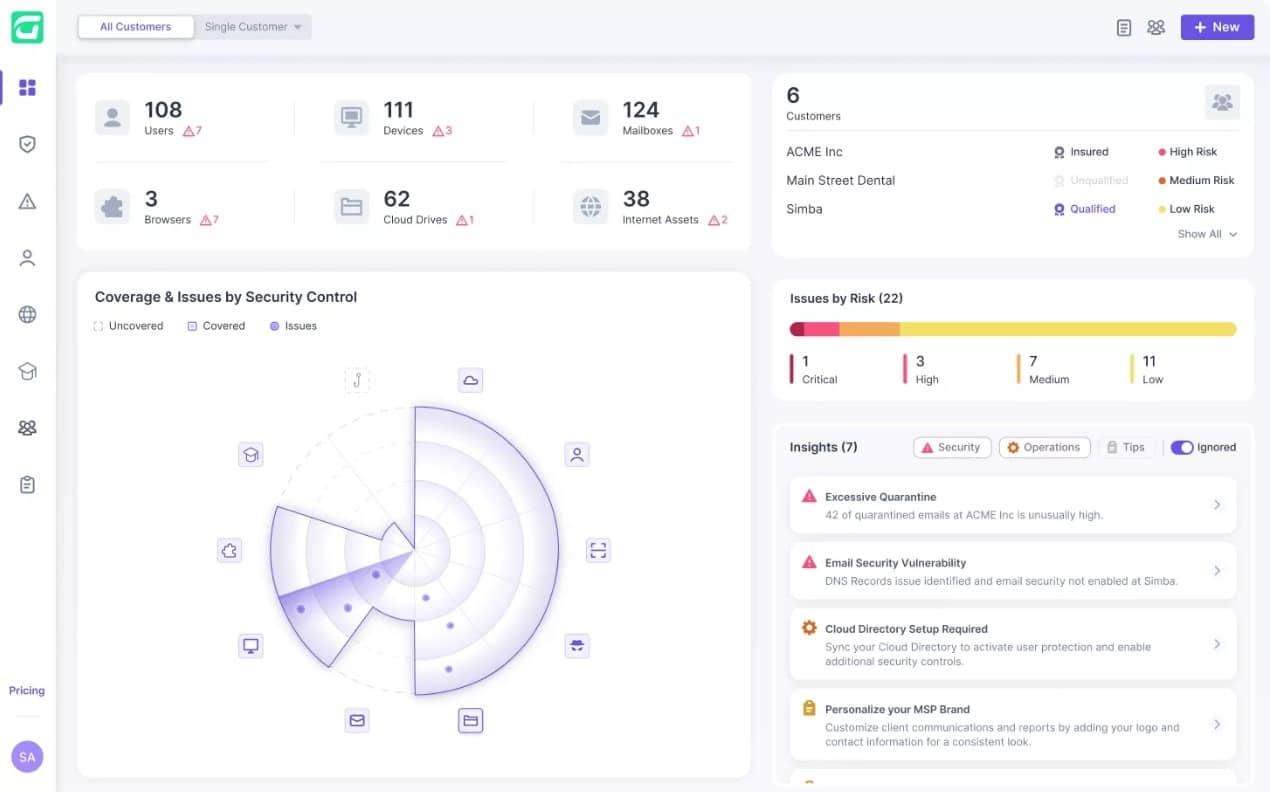
Guardz – FREE TRIAL
Email content scanning systems, such as Guardz, remove phishing emails as well as spam. Other threats that the Guardz system blocks are business email compromise (BEC), in which a con artist attempts to trick a clerk into sending money by pretending to be a company manager, and malware, which is often hidden in email attachments. To get a better understanding of how these systems work, you could access a 14-day free trial of Guardz.
In all, using email security software can make your emails more secure.
Implementing BYOD Policies
The growing use of personal devices for work also called Bring Your Own Device (BYOD), opens up a new set of security challenges for an organization. In particular, it gives the flexibility for users to work from anywhere and connect to any network, including public Wi-Fi. As an organization, you have to ensure that your employees never connect from public Wi-Fi as these are potential hotspots for attacks. Even connections through a mobile network must be highly limited and access must not be available for sensitive documents through a mobile device.
Formulating and enforcing BYOD policies is not easy, but at the same time sensitizing employees on these issues can be a good positive step forward.
Restrict Business Email Usage
Enforce security policies to prevent employees from sending personal emails through their business email addresses. Though this may seem silly, it can avoid many security issues for your organization as employees tend to use their most often checked email address for subscribing to newsletters, shopping sites, and other personal communication. Further, they may even publish/post their email on different forums, and all of these can greatly impact your organization’s security.
These public posts can give hackers the exact spelling of your employee’s email ID and it could be a matter of time to crack the password, especially if it doesn’t follow the established rules. Another potential problem is that personal email IDs are easier to hack. So, if a hacker takes control over a personal email ID, he or she can see the correspondence with your employee’s business email ID. Using this, the hacker can try to crack the password or send malware/phishing links to your network.
Due to these consequences, encourage your employees to restrict the use of their business emails for personal communication.
Use Encryption
For every email that is sent or received, there always exists the possibility of interception. In other words, an outbound email can be intercepted after it exits your network, and in all honesty, there’s nothing you can do about it.
The only option is to secure the contents of your email, so hackers can’t read it even if they manage to intercept the message. This can be achieved through encryption. What happens is that the contents of your email are converted into an unreadable bunch of characters using a code. A decryption code is given to the recipient and this can be used to decrypt the email content.
This way, no unauthorized person can decrypt the email and read through its contents.
Log Out of Emails
It’s a good practice to log out of emails once you’re done for the day. Though this can be a bit of inconvenience at first, your employees will get used to this practice, so make sure you encourage them to do so. You can even explore if there are other ways to automate this process depending on your employees’ work timings.
Thus, these are some of the business email security best practices that you can follow to keep your organization safe from phishing, malware, ransomware, and other attacks that use email as a vector. Remember, training employees and having them on board is the single most important strategy that must be followed continuously to ensure that any email security policy that you implement is effective.